🔐 CoinMerce 2026 Cracked Tool – Complete Security Analysis
The rapid expansion of the cryptocurrency market has created new opportunities for traders and investors worldwide. However, the increasing popularity of digital assets has also attracted cybercriminal activities targeting cryptocurrency platforms.
One tool frequently mentioned in underground forums is CoinMerce 2026, a cracked credential checking tool designed to test login combinations against crypto-related platforms.
Understanding how these tools work is essential for improving cybersecurity awareness and protecting cryptocurrency accounts.
🧩 What Is CoinMerce 2026 Cracked?
📌 Overview of the CoinMerce Checker Tool
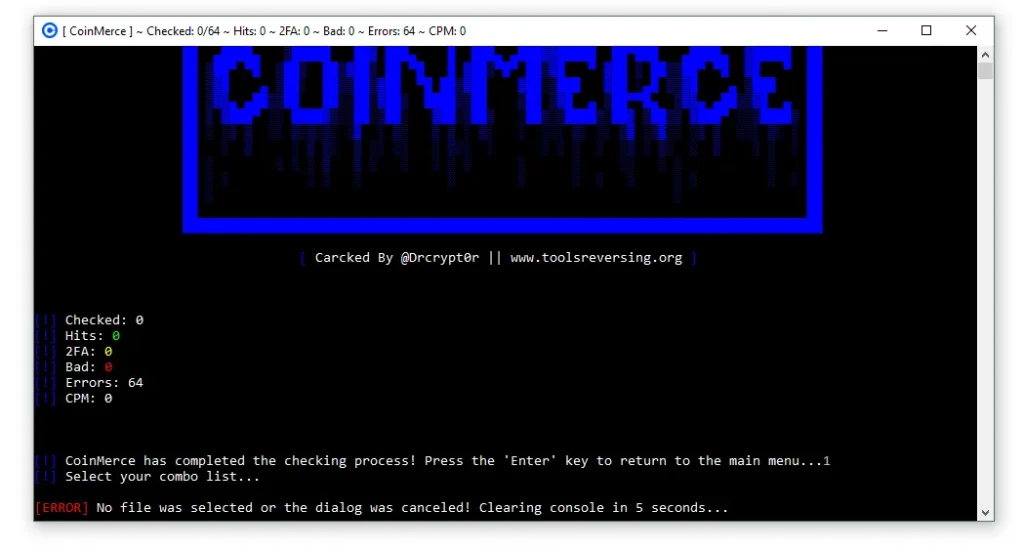
CoinMerce 2026 Cracked is described as an automated credential checking application used to test massive databases of leaked usernames and passwords.
These tools are commonly associated with credential stuffing attacks, where attackers attempt to log in using previously leaked credentials from data breaches.
⚙️ Key Characteristics
- 🤖 Automated credential testing system
- 📂 Supports large combo lists of email and password data
- 🔍 Identifies accounts with weak security protection
- 📊 Organizes results for further analysis
Because many users reuse passwords across platforms, such tools attempt to exploit this behavior.
⚡ Core Features of the CoinMerce Checker Tool
🚀 Multi-Thread Checking Engine
One of the primary features of CoinMerce 2026 Cracked is its multi-threaded processing capability, allowing it to run many login attempts simultaneously.
🔧 Functional Highlights
- ⚡ High-speed credential testing
- 🧵 Supports hundreds of parallel threads
- 📈 Improves checks-per-minute performance
This architecture enables rapid testing of thousands of credentials within a short period.
🌐 Proxy Integration System
To reduce detection risk, CoinMerce allows integration with external proxy servers.
🔗 Supported Proxy Types
- 🌍 HTTP proxies
- 🌍 SOCKS4 proxies
- 🌍 SOCKS5 proxies
🛡 Benefits of Proxy Usage
- 🕶 Hides real IP addresses
- 🚫 Helps bypass login rate limits
- 🌎 Enables distributed network requests
Proxy rotation is commonly used in large-scale automated login attempts.
📊 CoinMerce 2026 Cracked Account Result Classification
Instead of providing simple success or failure results, CoinMerce organizes login attempts into different categories.
📁 Result Types
✅ Hits (Valid Accounts)
- Valid login credentials
- Accounts accessible without additional security layers
🔐 2FA Protected Accounts
- Valid credentials
- Protected with two-factor authentication
❌ Bad Accounts
- Invalid login credentials
⚠️ Error Responses
- Proxy failures
- Network interruptions
- Platform rate limits
This classification allows users of such tools to review results more efficiently.
📂CoinMerce 2026 Cracked Automated Account Information Collection
When valid accounts are detected, the software may attempt to gather publicly accessible account data.
📑 Potential Extracted Information
- 📧 Email verification status
- 💰 Cryptocurrency wallet balances
- 📜 Transaction activity history
- 🔗 Linked wallet addresses
- 📅 Account creation details
All extracted information is typically saved into automatically generated log files.
🔁 Smart Retry Mechanism
CoinMerce also includes a retry system designed to reduce inaccurate results.
🔄 Retry System Functions
- 🔁 Reattempts accounts with unexpected responses
- ⚙ Handles temporary server issues
- 📉 Reduces false negative detections
This feature attempts to improve the reliability of credential testing results.
🛠 How Credential Checking Tools Operate
Tools like CoinMerce generally follow a structured workflow.
⚙️ Typical Attack Process
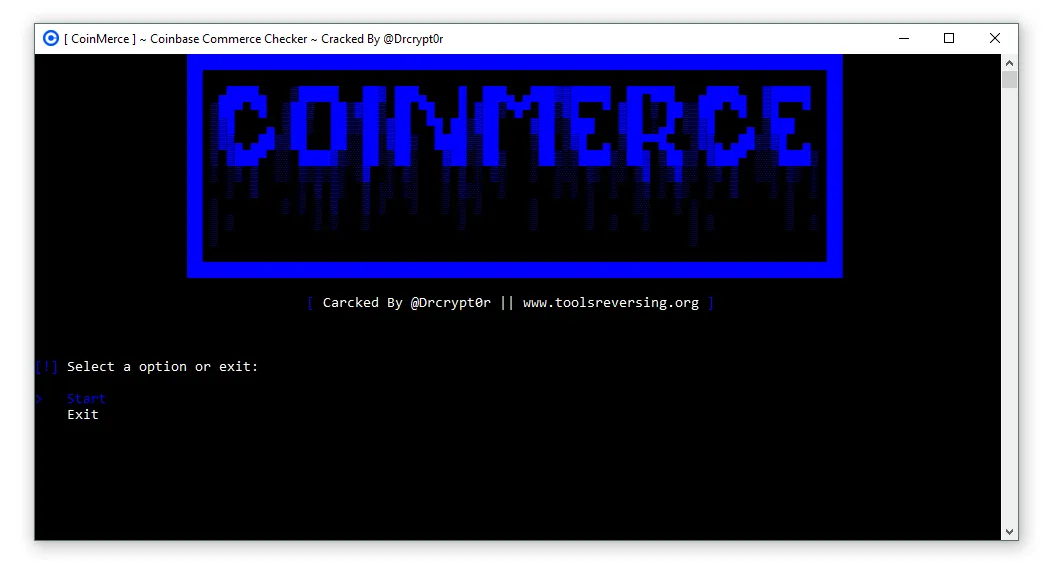
1️⃣ Launch the Tool
- 🖥 Open the software interface
- 📊 View dashboard and statistics panel
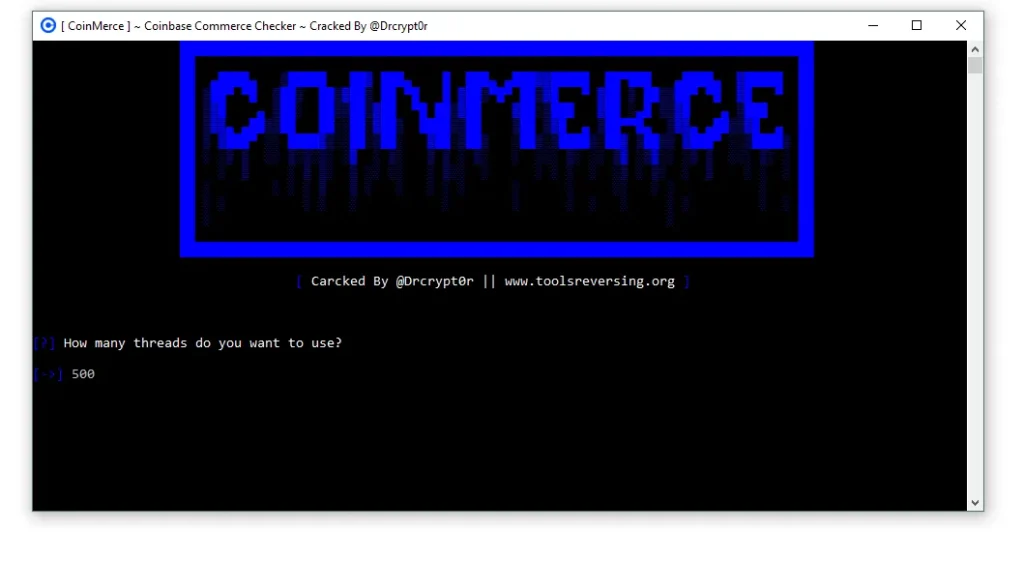
2️⃣ Configure Thread Settings
- 🧵 Select number of concurrent threads
- ⚡ Increase checking speed
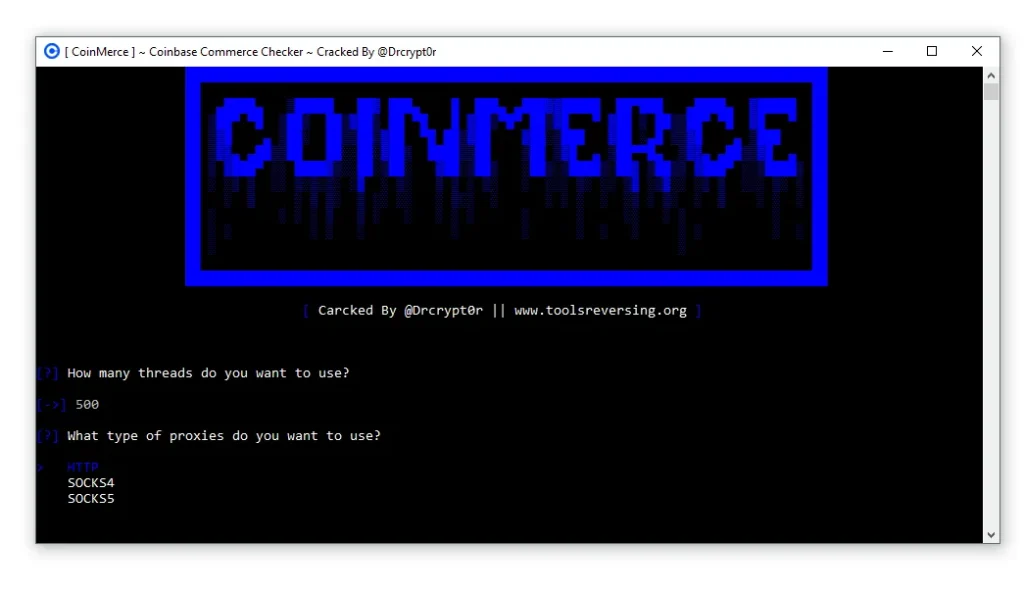
3️⃣ Load Proxy Servers
- 🌍 Import proxy lists
- 🕶 Hide real IP address
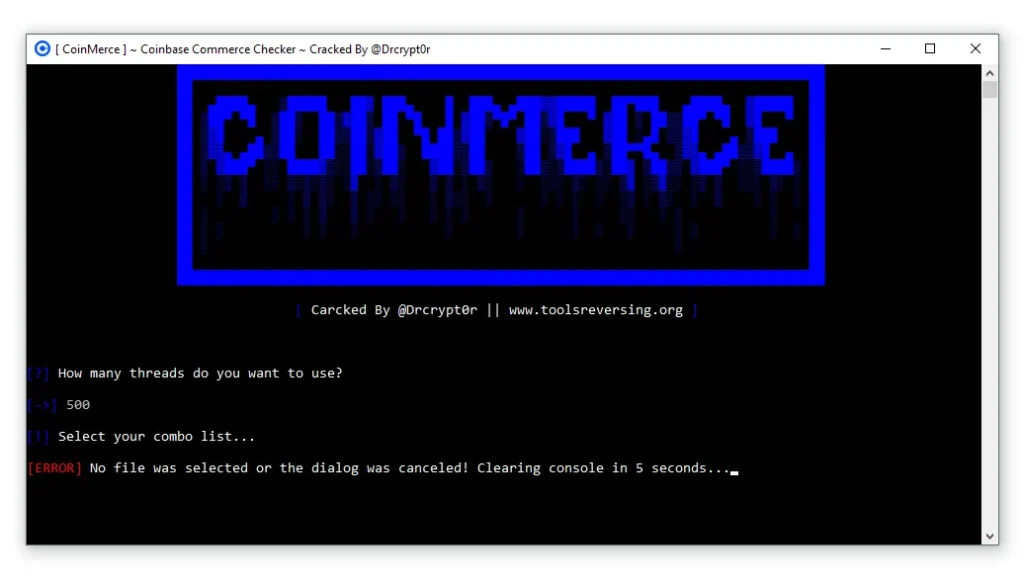
4️⃣ Upload Credential Lists
- 📂 Import combo lists containing email:password pairs
5️⃣ Start Automated Checking
- 🔍 Test login credentials against targeted platforms
6️⃣ Save Organized Results
- 📁 Store valid and invalid results in separate logs
🛡 Security Features Used by Cryptocurrency Platforms
To counter such threats, modern cryptocurrency platforms implement strong security measures.
🔐 Two-Factor Authentication (2FA)
Two-factor authentication adds an additional verification layer during account login.
📲 Common Authentication Methods
- 📱 Authenticator mobile applications
- 🔢 One-time verification codes
- 📷 QR code setup during account activation
Accounts protected with 2FA are significantly harder to compromise.
🔒 Secure Data Encryption
Sensitive information transmitted between users and platforms is encrypted.
🛡 Protected Data Includes
- 🔑 Login credentials
- 👤 Personal account information
- 💳 Financial transaction data
Encryption prevents attackers from intercepting sensitive information.
💰 Transaction Confirmation Systems
Cryptocurrency platforms often require additional verification before processing withdrawals.
🔎 Examples of Security Checks
- 📧 Email confirmation links
- 🔐 Authentication code verification
- 📱 Device recognition systems
These mechanisms help prevent unauthorized withdrawals.
🧠 Best Practices for Crypto Account Security
Cryptocurrency users should follow strong security practices to protect their accounts.
🔑 Use Strong and Unique Passwords
Avoid reusing passwords across different platforms.
🛠 Password Security Tips
- 🔢 Use long passwords with numbers and symbols
- 🔐 Avoid predictable words
- 📦 Store passwords in a password manager
🔐 Enable Two-Factor Authentication
Always activate two-factor authentication whenever available.
📍 Recommended Platforms for 2FA
- 🪙 cryptocurrency exchanges
- 📊 trading platforms
- 👛 crypto wallets
- 💳 financial services
👀 Monitor Account Activity
Regularly reviewing account activity helps detect suspicious behavior early.
🔎 Monitor These Areas
- 🌍 login locations
- 💸 withdrawal history
- 📱 connected devices
- 🔗 API access permissions
🧊 Store Large Assets in Hardware Wallets
Hardware wallets offer enhanced protection for long-term crypto storage.
🛡 Hardware Wallet Benefits
- 🔒 Offline private key storage
- 🌐 Protection against online attacks
- 📦 Safe long-term asset management
⚖ Legal and Ethical Considerations
Unauthorized access to digital accounts may violate cybersecurity laws in many countries.
⚠ Potential Legal Violations
- 🚫 unauthorized system access
- ⚖ computer fraud laws
- 💻 cybersecurity regulation breaches
Users should always follow legal guidelines and platform policies.
Download CoinMerce 2026 cracked
🧾 Final Thoughts about CoinMerce 2026 Cracked
The appearance of tools like CoinMerce 2026 cracked demonstrates the growing cybersecurity challenges within the cryptocurrency ecosystem.
While automated credential testing tools attempt to exploit weak passwords and reused credentials, users can significantly reduce risks by implementing strong security practices.
Maintaining good password hygiene, enabling two-factor authentication, and monitoring account activity are essential steps in protecting cryptocurrency investments.
❓ FAQ
🔍 What is CoinMerce 2026 cracked tool?
CoinMerce 2026 Cracked is described as a credential checking tool designed to test leaked login combinations against online services.
🔐 How do credential stuffing attacks work?
Credential stuffing attacks use automated tools to test previously leaked usernames and passwords across multiple platforms.
🛡 How can users protect cryptocurrency accounts?
Users should enable two-factor authentication, create strong passwords, and monitor account activity regularly.
⚖ Is using credential checking tools legal?
Using such tools to access accounts without authorization may violate cybersecurity laws in many jurisdictions.