The rise of advanced cyber threats has made Remote Access Trojans (RATs) one of the most dangerous tools in modern cybercrime. Among them, SiriusQT RAT 2026 stands out as a powerful, feature-rich malware suite designed for surveillance, data theft, and complete system control.
🧠 What is SiriusQT RAT 2026?
SiriusQT RAT 2026 is a sophisticated malware framework that enables attackers to remotely access and control infected systems. It combines multiple attack vectors into one platform, including surveillance tools, credential harvesting, and stealth persistence mechanisms.
🔍 Key Characteristics:
- Advanced remote control capabilities
- Data exfiltration and credential theft
- Multi-layered persistence techniques
- Integration with modern communication channels
- Modular and customizable payload builder
Unlike basic malware, SiriusQT RAT 2026 operates as a complete cyberattack ecosystem, making it particularly dangerous for both individuals and organizations.
⚙️ Automated Attack Execution System
⚡ Auto Tasks Engine feature of SiriusQT RAT 2026
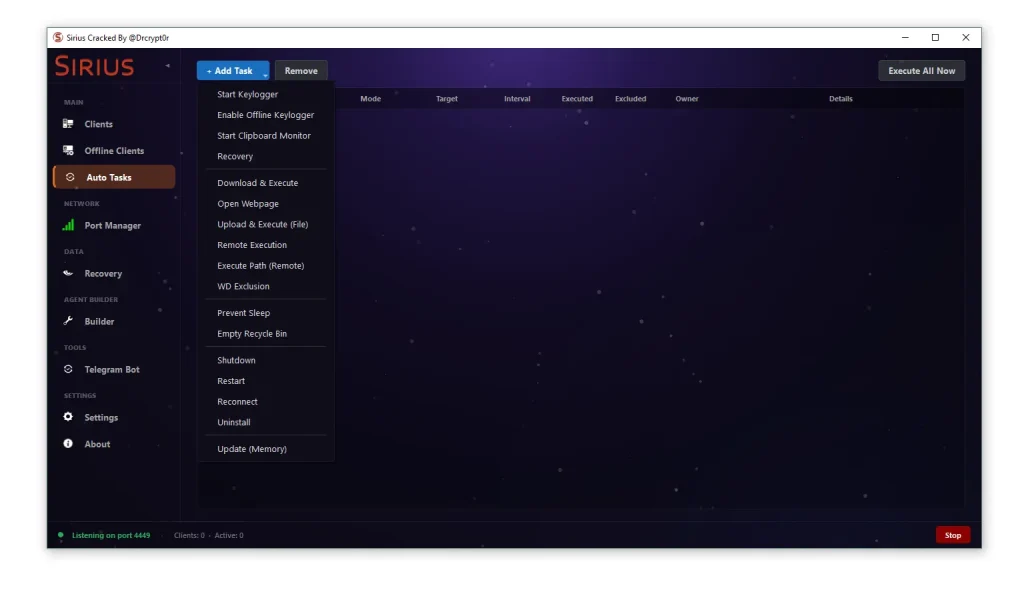
- Automated Keylogging & Data Capture:
This feature records every keystroke entered on the infected system, including passwords, emails, and private messages. It can operate even when the device is offline, storing logs locally and sending them later. This makes it extremely effective for long-term surveillance. Attackers often use this to access banking credentials or corporate accounts without triggering immediate alerts. Over time, this creates a detailed behavioral profile of the victim, increasing the value of stolen data significantly. - Clipboard Monitoring & Data Interception:
Clipboard tracking allows attackers to capture anything copied by the user, including sensitive information like crypto wallet addresses or confidential documents. In many cases, attackers replace copied wallet addresses with their own, leading to financial theft. This technique is especially dangerous because it operates silently and exploits user trust. Victims often don’t realize the manipulation until funds are lost. - Remote Payload Execution:
This functionality enables attackers to download and execute additional malicious files directly on the victim’s system. These payloads may include ransomware, spyware, or backdoors. It essentially turns the infected device into a launchpad for further attacks. This layered approach increases attack success rates and makes detection more difficult. - System Manipulation Commands:
Attackers can remotely shut down, restart, or keep the system active. Preventing sleep mode ensures continuous monitoring or cryptomining operations. These controls also allow attackers to disrupt normal operations, particularly in corporate environments. Such actions can cause downtime, productivity loss, and financial damage.
🏗️ Payload Builder & Customization
🧩 Builder Module of SiriusQT RAT 2026
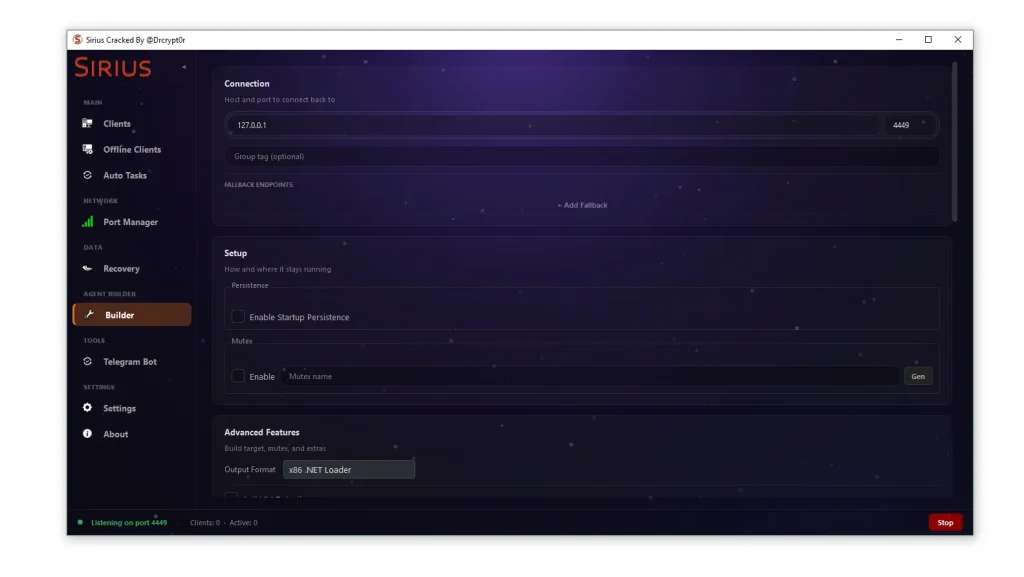
- Custom Command & Control Configuration:
Attackers can define server addresses and ports for communication between the infected system and their control panel. This flexibility allows them to evade detection by changing infrastructure frequently. Multiple fallback servers ensure uninterrupted control even if one server is blocked. This redundancy significantly improves attack resilience. - Persistence Mechanisms:
The RAT can automatically restart after system reboot using registry keys or scheduled tasks. This ensures long-term access without requiring reinfection. Persistence is one of the most critical aspects of modern malware, as it allows attackers to maintain control for extended periods. - Stealth & Anti-Detection Techniques:
Features like mutex creation prevent multiple instances from running, reducing suspicion. The use of memory-based execution avoids writing files to disk, making traditional antivirus tools less effective. These techniques are commonly used in advanced persistent threats (APTs). - Flexible Output Formats:
The builder supports multiple payload formats, including executable files and script-based loaders. This allows attackers to tailor the malware to different environments and security configurations. It also increases the chances of bypassing detection systems.
🖥️ Remote Control Dashboard
🎯 Client Management System in SiriusQT RAT 2026
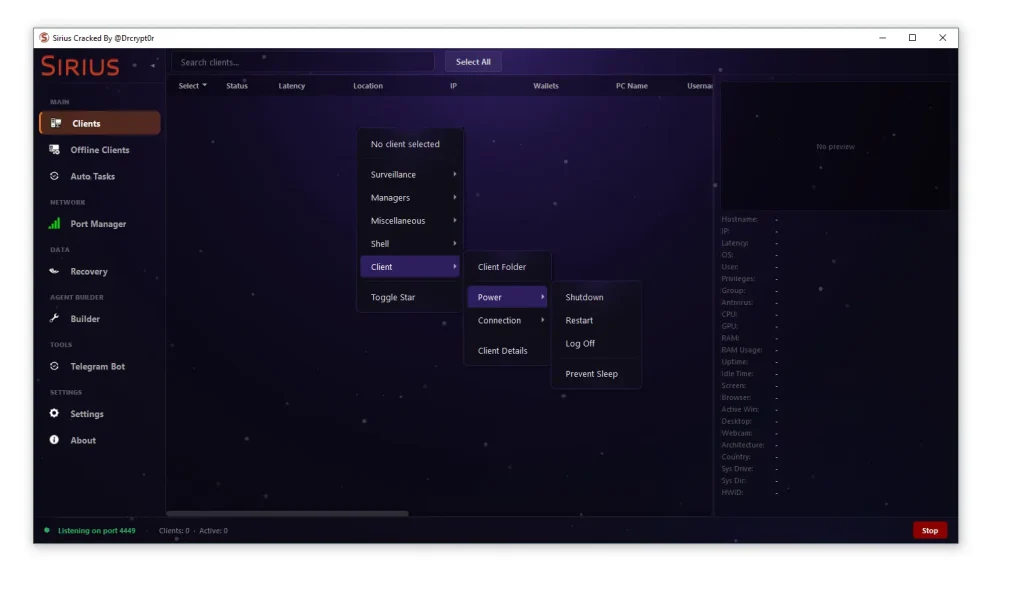
- Real-Time System Monitoring:
Attackers can view detailed information about infected devices, including location, IP address, and system specifications. This helps prioritize high-value targets such as corporate machines or financial systems. Real-time data enables quick decision-making during attacks. - Surveillance Capabilities:
Webcam access, microphone recording, and screen capture allow full monitoring of user activity. This level of surveillance can compromise privacy and expose sensitive information. In corporate settings, it may lead to intellectual property theft. - File & Process Management:
Attackers can browse files, terminate processes, and manage system resources remotely. This enables them to remove security tools or extract valuable data. It also allows for deeper system manipulation without physical access. - Command Execution Interface:
Integrated command-line tools provide complete control over the system. Attackers can execute scripts, install additional malware, or modify system settings. This makes the RAT highly versatile and dangerous.
🛠️ System Management & Exploitation Tools
🧰 Advanced Control Features
- Process Injection & Manipulation:
Attackers can inject malicious code into legitimate processes, making detection extremely difficult. This technique hides malware within trusted applications. It is commonly used in sophisticated cyberattacks. - Task Scheduling Exploitation:
Creating scheduled tasks ensures repeated execution of malicious actions. This can be used to maintain persistence or automate attacks. It also reduces the need for manual intervention. - Network Monitoring & Control:
Viewing active connections allows attackers to identify additional targets within the same network. This can lead to lateral movement and broader compromise. It is especially dangerous in enterprise environments. - Security Policy Modification:
The RAT can disable security features like firewalls or user account controls. This weakens system defenses and makes further exploitation easier. It also prevents detection by standard security tools.
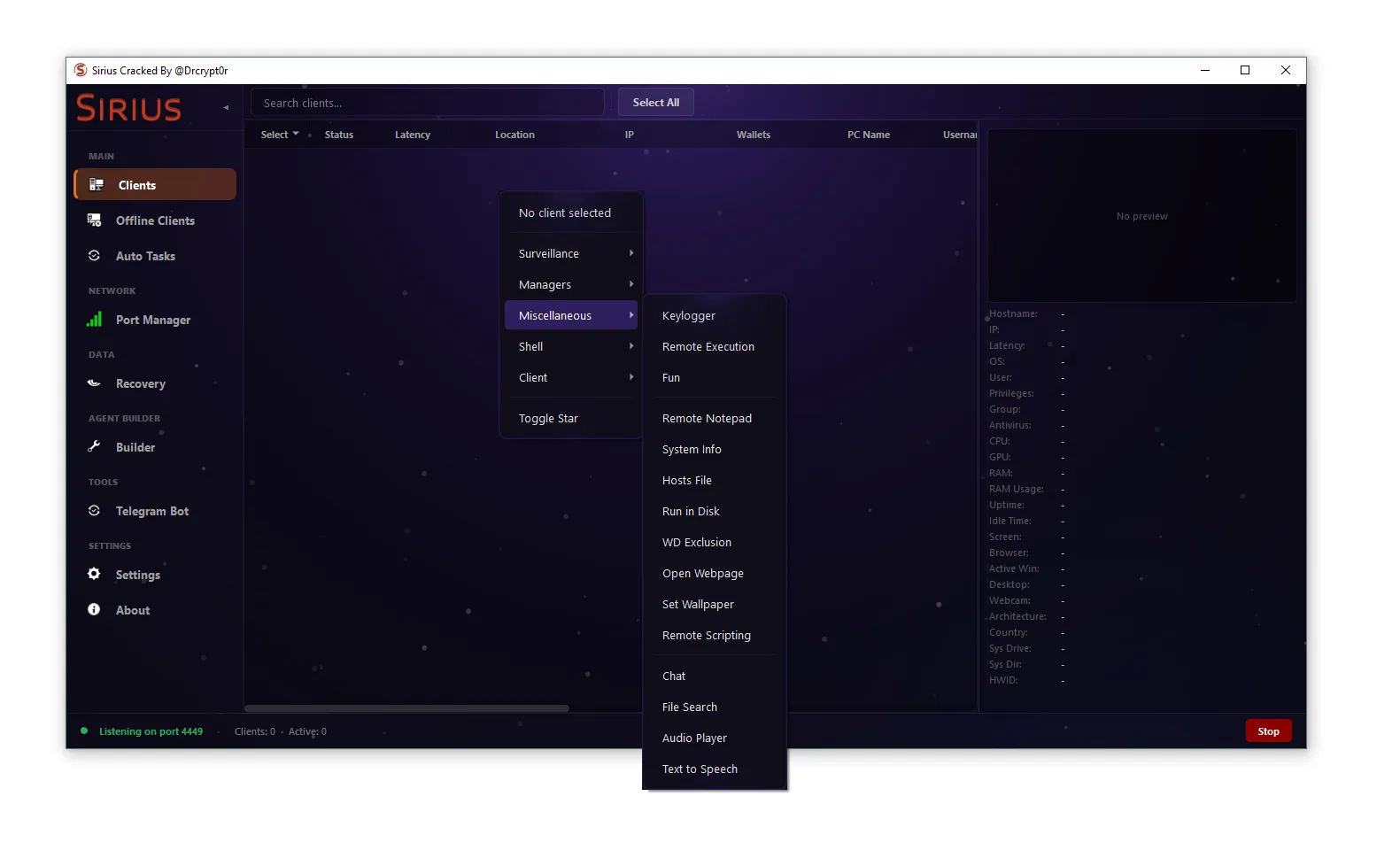
🎭 Miscellaneous Exploitation Features
🎵 Additional Tools of SiriusQT RAT 2026
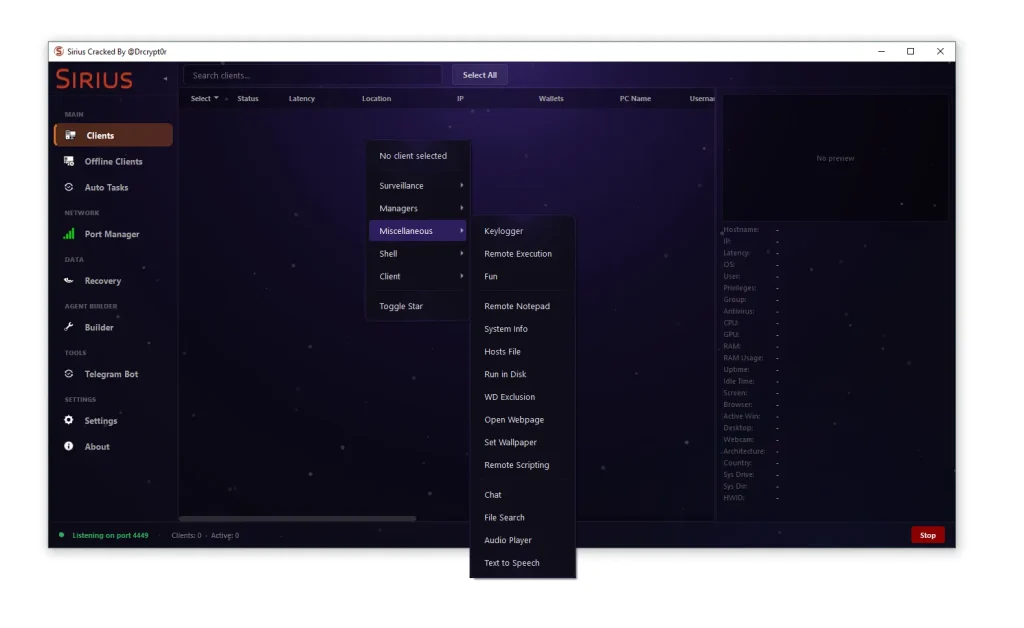
- Social Engineering Capabilities:
Features like chat messaging and fake notifications allow attackers to manipulate victims directly. This can lead to credential disclosure or execution of malicious actions. Social engineering remains one of the most effective attack methods. - Hosts File Manipulation:
Redirecting websites can lead users to phishing pages without their knowledge. This is often used to steal login credentials. It can also block access to security updates or antivirus services. - File Search & Data Discovery:
Attackers can scan for specific file types such as documents or wallet files. This helps them quickly locate valuable data. Targeted searches increase efficiency and reduce detection risk. - Audio & Visual Manipulation:
Playing sounds or changing wallpapers can be used for intimidation or pranks. In ransomware attacks, these features are often used to display warnings or demands.
🌐 Network & Communication Control
📡 Port Manager in SiriusQT RAT 2026
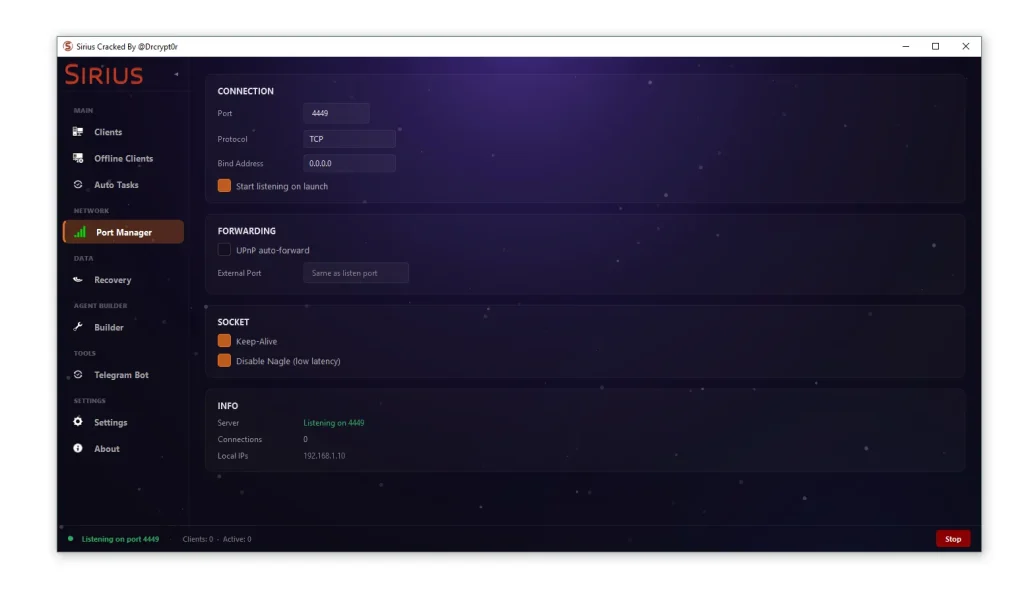
- Custom Port Configuration:
Attackers can use non-standard ports to avoid detection. This makes it harder for firewalls to identify malicious traffic. Custom ports also allow better control over network behavior. - Automatic Port Forwarding:
UPnP technology enables automatic router configuration, simplifying setup. This is particularly useful for attackers with limited networking knowledge. It increases accessibility of the tool. - Persistent Connections:
Keep-alive settings ensure continuous communication between attacker and victim. This reduces the chances of losing control. It also enables real-time monitoring. - Low Latency Optimization:
Disabling certain network delays improves responsiveness. This is essential for live surveillance and interactive control. It enhances the overall effectiveness of the RAT.
🔓 Data Theft & Credential Recovery
💾 Recovery Module in SiriusQT RAT 2026
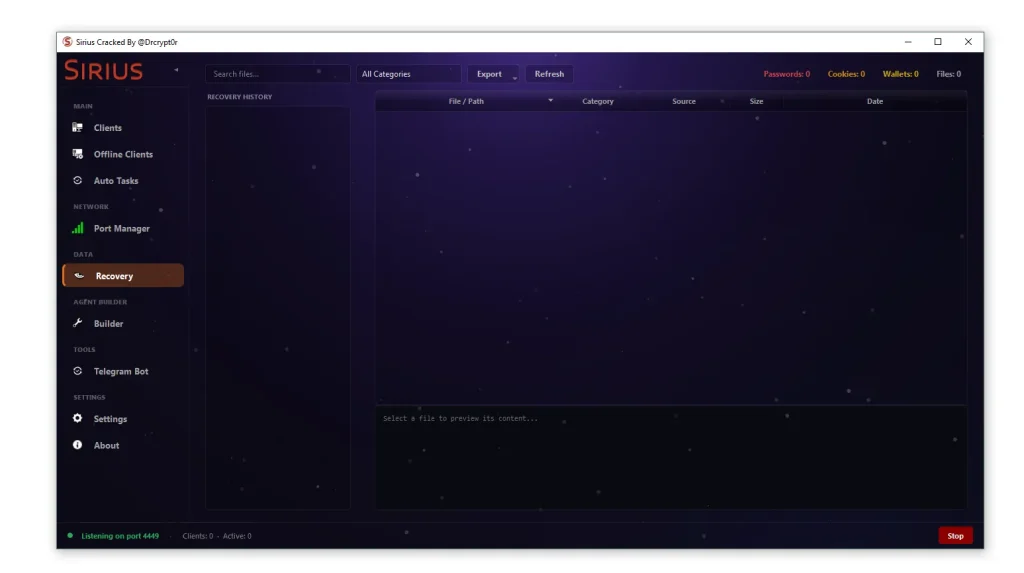
- Browser Credential Extraction:
The RAT can retrieve saved passwords from popular browsers. This includes login credentials for email, banking, and social media accounts. Such data is highly valuable on the dark web. - Session Hijacking via Cookies:
Stolen cookies allow attackers to bypass login authentication. This provides direct access to user accounts without needing passwords. It is a powerful technique for account takeover. - Financial Data Harvesting:
Autofill data, including credit card details, can be extracted بسهولة. This information is often used for fraud or identity theft. Victims may face severe financial consequences. - Crypto Wallet Theft:
The malware scans for wallet files and private keys. This enables attackers to steal digital assets directly. Cryptocurrency theft is one of the primary motivations behind such malware.
🖥️ Remote Shell Access
💻 Command Execution in SiriusQT RAT 2026
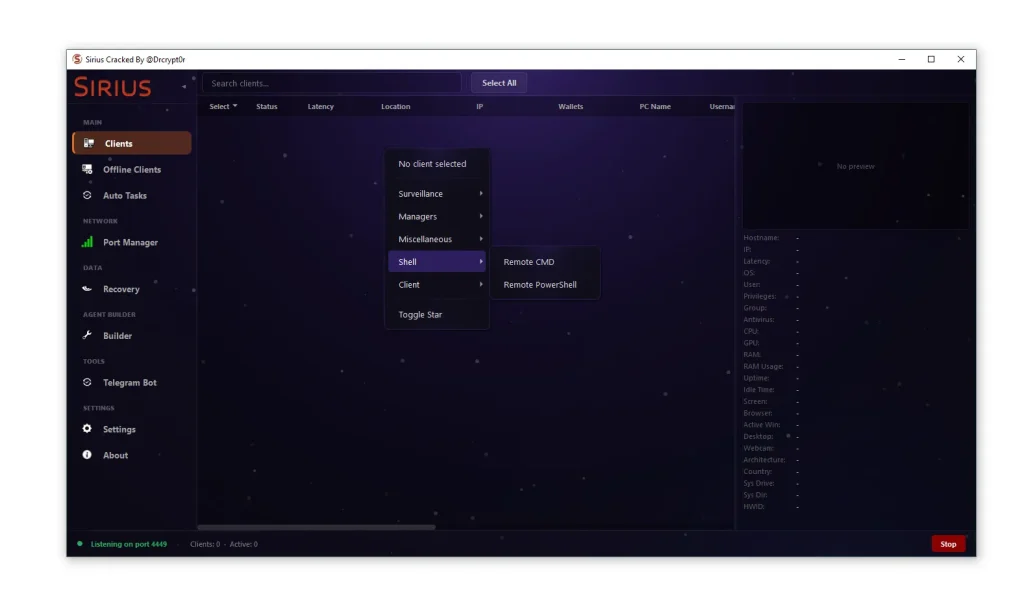
- Command Prompt Control:
Provides basic system control through traditional command-line interface. Attackers can execute commands, manage files, and configure settings. It is simple but highly effective. - PowerShell Exploitation:
Offers advanced scripting capabilities for complex operations. PowerShell can be used for fileless attacks and system automation. It is widely used in modern cyber threats.
👁️ Surveillance & Monitoring
🎥 Spy Features of SiriusQT RAT 2026
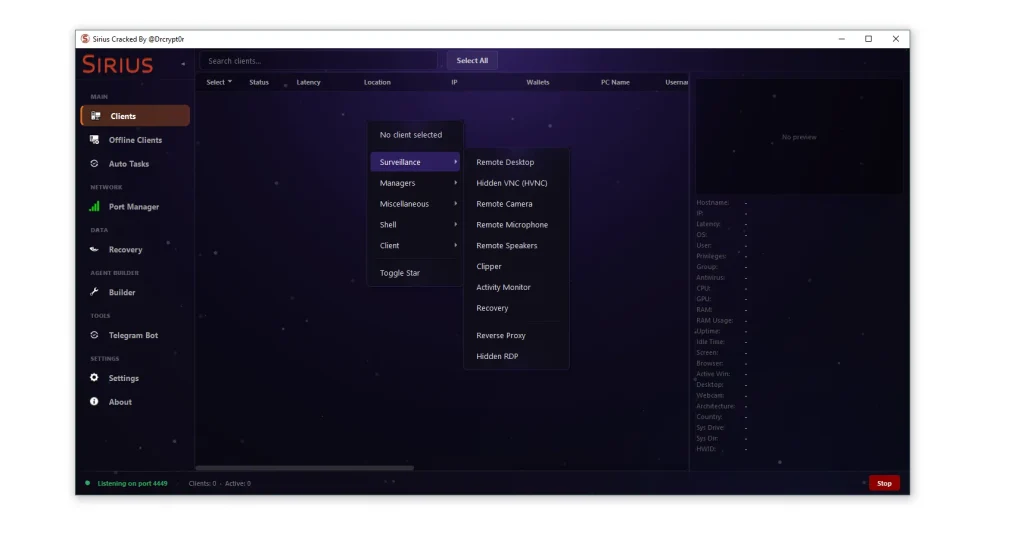
- User Activity Tracking:
Records applications, browsing activity, and system usage. This provides valuable insights into user behavior. It helps attackers plan targeted attacks. - Hidden Remote Access:
Enables access without notifying the user. This ensures stealth and reduces detection risk. Victims often remain unaware of the intrusion. - Proxy Functionality:
Allows attackers to route traffic through the infected system. This hides their identity and location. It is often used for further attacks.
📱 Telegram-Based Control System
🤖 Modern C2 Integration of SiriusQT RAT 2026
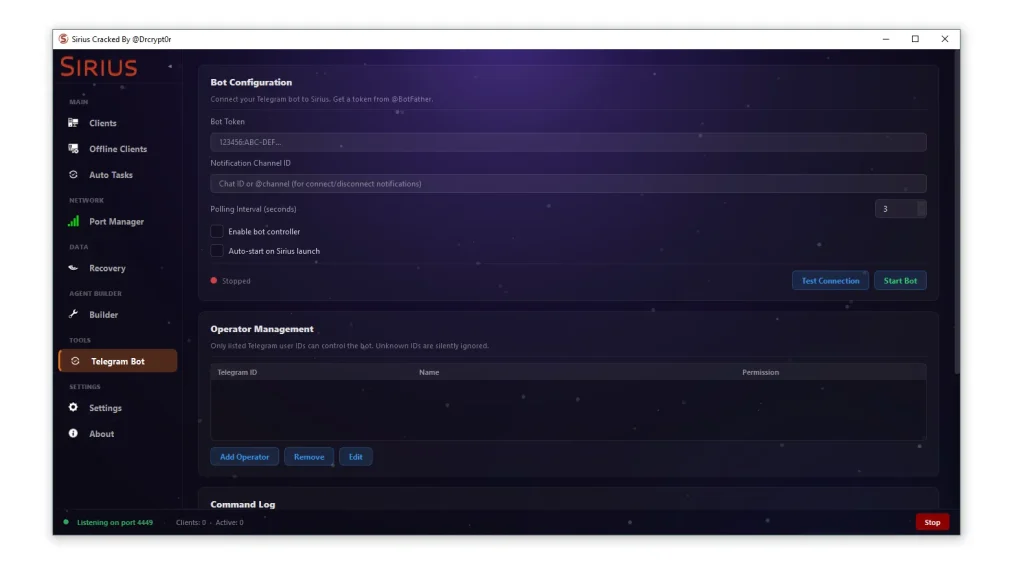
- Remote Command Execution via Messaging:
Attackers can control infected systems using a messaging platform. This provides convenience and mobility. Commands can be sent from anywhere. - Real-Time Notifications:
Alerts are sent when systems connect or disconnect. This helps maintain control and monitor activity. It also provides quick response capability. - Access Control Management:
Only authorized users can interact with the system. This prevents unauthorized takeover by other attackers. It adds a layer of operational security.
⚠️ Security Risks & Indicators of Compromise
🚨 Warning Signs
- Unusual Network Activity:
Unexpected outbound connections on uncommon ports may indicate infection. Monitoring network traffic is essential for detection. - Suspicious System Behavior:
Slow performance, unknown processes, or disabled security tools can signal compromise. Regular system audits help identify issues early. - Unauthorized Changes:
Modifications to registry settings or firewall rules are red flags. These changes often indicate persistence mechanisms.
🛡️ How to Protect Against SiriusQT RAT 2026
🔐 Best Practices
- Use Advanced Security Solutions:
Deploy endpoint detection and response (EDR) tools. These provide real-time monitoring and threat detection. - Restrict Script Execution:
Limit the use of PowerShell and other scripting tools. This reduces attack surface significantly. - Monitor Network Traffic:
Analyze outbound connections for anomalies. Early detection can prevent major damage. - User Awareness Training:
Educate users about phishing and malware risks. Human error is a major entry point for attacks.
Download SiriusQT RAT 2026
🧾 Conclusion
SiriusQT RAT 2026 represents a new generation of cyber threats that combine multiple attack techniques into a single platform. Its advanced features, stealth capabilities, and flexible deployment make it a serious risk for both individuals and organizations.
Understanding how such malware operates is the first step toward effective defense. By implementing strong security practices and staying informed, users can significantly reduce their risk of infection.
❓ FAQs
❓ What is SiriusQT RAT 2026 used for?
SiriusQT RAT 2026 is used by attackers to remotely control systems, monitor activity, and steal sensitive data without user consent.
❓ Is SiriusQT RAT 2026 dangerous for businesses?
Yes, it poses significant risks including data breaches, financial loss, and operational disruption in corporate environments.
❓ How does SiriusQT RAT 2026 avoid detection?
It uses stealth techniques like memory execution, encrypted communication, and disabling security tools.
❓ Can antivirus software detect it?
Advanced security solutions may detect it, but traditional antivirus tools can struggle due to its sophisticated evasion methods.
❓ What are the common signs of infection?
Unusual network activity, slow performance, and unauthorized system changes are common indicators.
❓ How can I protect my system?
Use updated security tools, monitor network traffic, and avoid downloading suspicious files or software.
❓ Why is the cracked version more risky?
Cracked versions may contain hidden backdoors, exposing even attackers to additional threats.
❓ Is it legal to use such tools?
No, using or distributing RATs without authorization is illegal in most countries.