🛡️ Raton RAT 2026 Cracked: The Ultimate Feature-Rich Remote Access Tool of the Year
Remote Access Trojans (RATs) have become one of the most advanced and dangerous forms of malware in today’s digital ecosystem. With the rise of sophisticated cyber threats, tools like Raton RAT 2026 Cracked demonstrate how attackers combine stealth, persistence, and multi-functional capabilities into a single framework. This evolution reflects broader trends in cybersecurity, where malware is no longer simple but highly modular and adaptive.
For businesses and individuals across the United States and Europe, understanding such threats is critical. Cyberattacks are no longer limited to large corporations—small businesses, freelancers, and even personal users are equally targeted. Raton RAT 2026 Cracked represents a new generation of threats that can bypass traditional security systems and maintain long-term access to compromised devices.
⚙️ Builder Execution Option
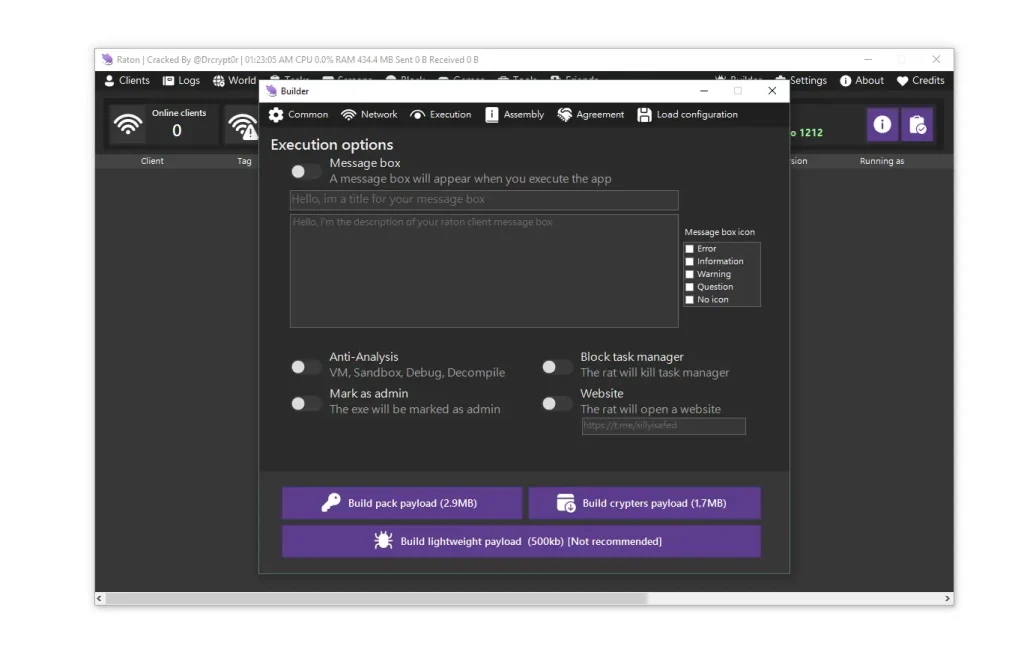
- ⚡ Custom Message Box:
This feature of Raton RAT 2026 Cracked allows the payload to display a customized message box upon execution, often designed to mimic legitimate software alerts or system notifications. Attackers use this technique as part of social engineering strategies to build trust and reduce suspicion. For example, a fake software update or system warning may appear, encouraging the user to proceed without hesitation. This tactic is particularly effective against non-technical users who rely on visual cues for trust. From a cybersecurity perspective, recognizing such deceptive interfaces is crucial. Organizations should implement application whitelisting and restrict execution of unknown files. Users should be trained to verify the authenticity of popups before interacting with them. Advanced endpoint protection tools can detect unusual execution behavior even when the interface appears legitimate. This feature highlights the importance of combining technical defenses with user awareness. - 🛑 Anti-Analysis (VM, Sandbox, Debuggers, Decompilers):
Raton RAT 2026 Cracked integrates multiple anti-analysis techniques to evade detection during security testing. These mechanisms detect whether the malware is running in a virtual machine, sandbox, or debugging environment. If such conditions are identified, the malware may stop execution or alter its behavior to avoid exposure. This significantly complicates the work of cybersecurity researchers and delays the development of detection signatures. Modern security solutions must rely on behavioral analysis rather than static signatures to counter such threats. Organizations should deploy advanced endpoint detection and response systems that monitor real-time activity. Continuous threat intelligence updates are essential to identify new evasion techniques. This feature demonstrates how attackers are adapting to defensive technologies, making proactive security measures more important than ever. - 🔐 Mark as Admin:
The ability to request administrative privileges allows the malware to gain elevated access to system resources. Once granted, it can modify system configurations, disable security tools, and establish persistence mechanisms. This level of access significantly increases the potential damage, as attackers can execute commands without restriction. Users should exercise caution when granting admin permissions, especially to unknown applications. Enterprises should enforce least-privilege policies to limit access rights. Monitoring privilege escalation attempts can help detect suspicious activity early. Security systems should log and alert administrators when unauthorized elevation occurs. This feature underscores the importance of strict access control in modern cybersecurity environments. - 🚫 Block Task Manager:
Blocking Task Manager prevents users from viewing or terminating malicious processes, allowing the malware to operate undetected. This tactic is commonly used to maintain control and avoid user intervention. If Task Manager fails to open or behaves abnormally, it may indicate a compromised system. Users should treat such behavior as a warning sign and take immediate action. Organizations should deploy monitoring tools capable of detecting process manipulation. Incident response teams must be prepared to isolate affected systems quickly. This feature highlights the importance of system-level monitoring and rapid response strategies. - 🌐 Website Launch:
Automatically launching a predefined website upon execution is often used to redirect users to phishing pages or malicious content. This can be used to collect credentials or deliver additional payloads. For example, users may be directed to a fake login page that captures sensitive information. Web filtering solutions can help block access to suspicious domains. Users should avoid entering personal data on unfamiliar websites. Regular security awareness training can reduce the effectiveness of such tactics. This feature demonstrates how malware combines technical and social engineering techniques to achieve its goals.
🌐 Builder Network
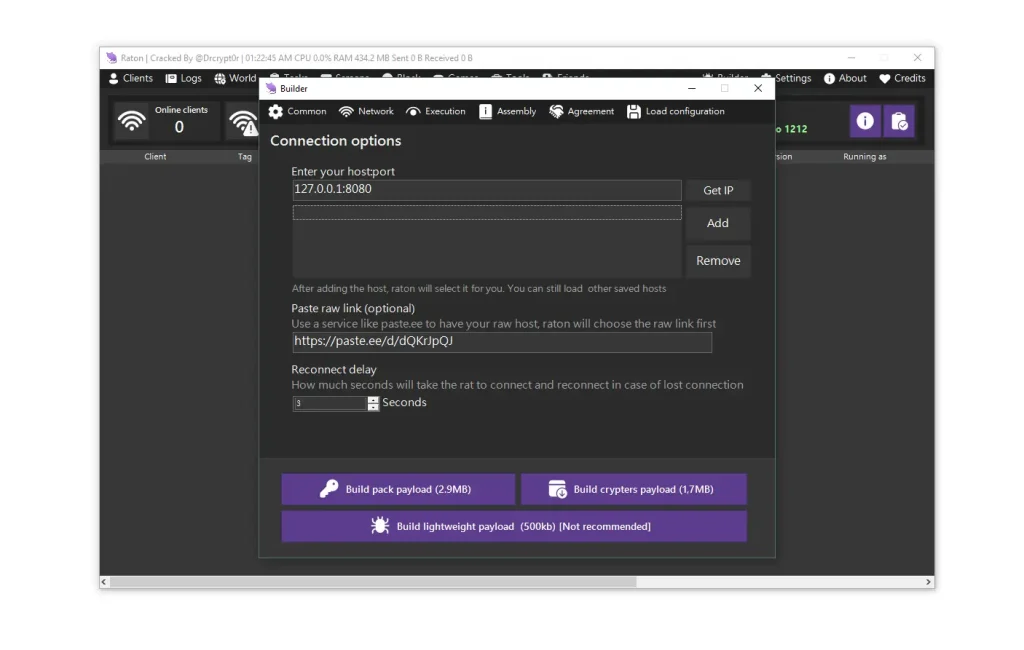
- 🔗 Host/Port Management:
This feature allows attackers to configure multiple command-and-control servers, ensuring continuous communication with infected systems. If one server is taken down, another can take over, maintaining persistence. This redundancy makes it difficult for security teams to disrupt operations completely. Network administrators should monitor outbound traffic for unusual connections. Firewalls and intrusion detection systems can help block suspicious activity. Logging network traffic is essential for forensic analysis. This feature highlights the importance of network-level security in detecting advanced threats. - 📡 Raw Pastebin Link (Dynamic C2):
Dynamic configuration using external sources allows attackers to update server details without modifying the malware itself. This makes it harder to block communication permanently. Security teams should monitor DNS queries and restrict access to suspicious domains. Advanced threat detection systems can identify patterns associated with dynamic command-and-control communication. Regular updates to security tools are necessary to stay ahead of evolving threats. This feature demonstrates the adaptability of modern malware. - ⏱️ Reconnect Delay:
The reconnect delay mechanism ensures the malware continuously attempts to re-establish communication with its server. This persistence can generate unusual network traffic patterns, which can be detected by anomaly-based systems. Organizations should configure alerts for repeated connection attempts. Blocking suspicious IP addresses can disrupt communication. Continuous monitoring is essential for early detection and response. - 📦 Build Types (Pack, Crypted, Lightweight):
Different build options allow attackers to balance stealth and functionality. Packed versions include full features, while crypted versions focus on evasion. Lightweight builds are smaller and harder to detect but offer limited capabilities. Security tools must be capable of detecting all variants. Regular updates and threat intelligence integration are crucial. Understanding these variations helps improve defense strategies.
⚙️ Builder Server Options
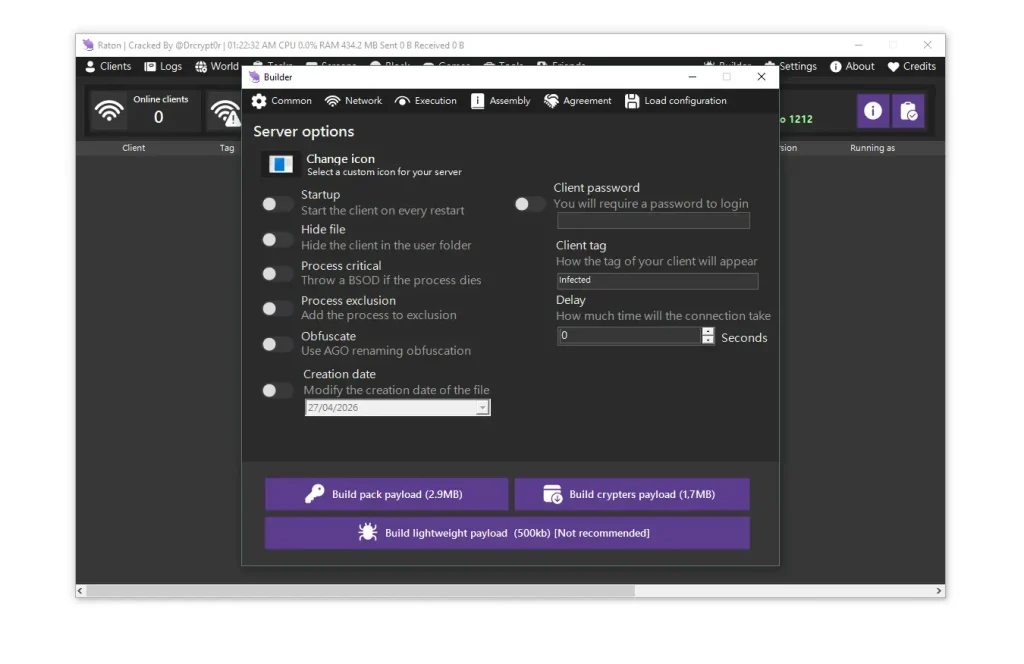
- 🎭 Custom Icon:
Using custom icons allows malware to mimic legitimate software, increasing the likelihood of execution. Users should verify file authenticity before opening. Organizations should enforce software verification policies. Digital signatures can help confirm legitimacy. Awareness training is essential to prevent deception. - 🔄 Startup Persistence:
Ensures the malware runs automatically after system reboot, maintaining long-term access. Regular audits of startup entries can help detect unauthorized programs. Endpoint management tools can monitor changes. Removing suspicious entries promptly is crucial. - 🕵️ Hide File:
Hiding files in system directories makes detection difficult. Users should enable hidden file visibility when investigating issues. Security tools can scan hidden directories for anomalies. Regular scans improve detection rates. - ⚠️ Process Critical:
Making a process critical can crash the system if terminated, discouraging removal attempts. Specialized tools are required to safely remove such processes. Monitoring system behavior is essential. - 🧬 Process Exclusion & Obfuscation:
Adding exclusions and obfuscating code helps malware evade antivirus detection. Behavior-based detection systems are more effective against such tactics. Regular updates to security tools are necessary. - 📅 Date Mutilation:
Altering file timestamps helps malware blend with legitimate files. Forensic analysis should verify file metadata. This technique complicates investigations. - 🔑 Client Password, Tag & Delay:
These features help attackers manage infected systems efficiently. They highlight the organized nature of modern cyber threats. Monitoring unusual identifiers can aid detection.
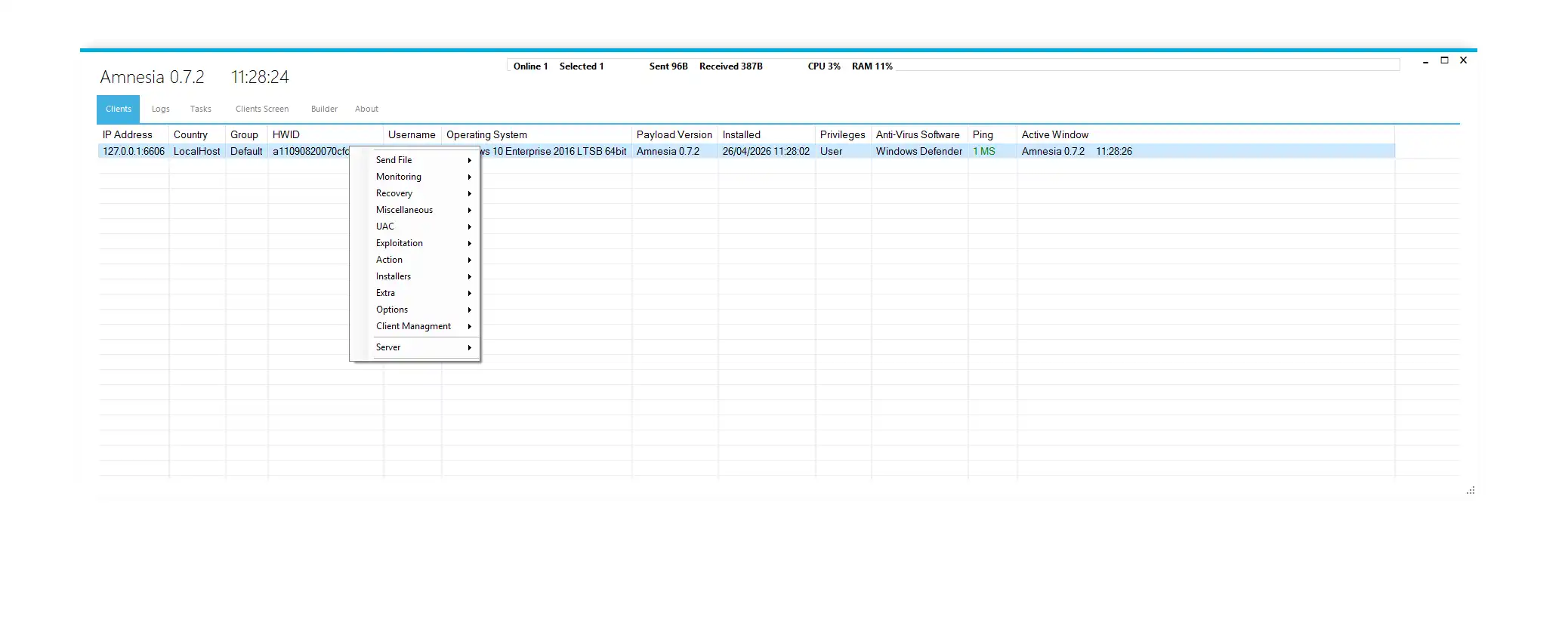
🖥️ Client Control Features
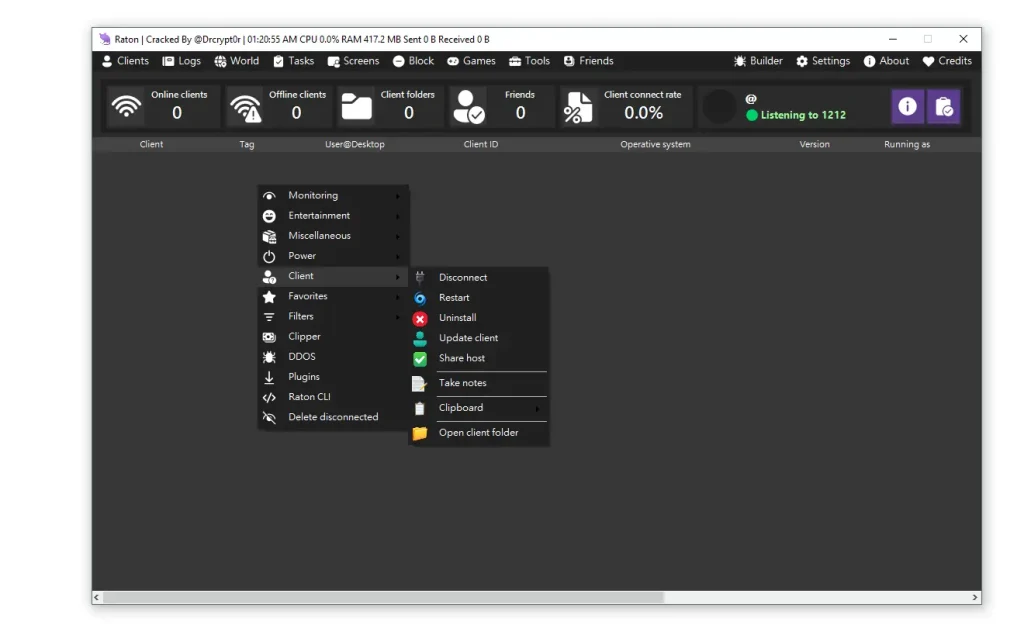
- 📊 Real-Time Dashboard & Controls:
The client control panel provides a centralized dashboard showing active and inactive systems, connection status, and system details. This allows attackers to manage multiple devices efficiently and execute commands in real time. Features like monitoring, restarting, uninstalling, and accessing system files give full control over infected machines. Clipboard access enables capturing sensitive data such as passwords or financial details. Security teams should monitor for unauthorized remote access and unusual system behavior. Implementing endpoint detection tools can help identify such activities. This feature demonstrates the importance of centralized control in modern cyberattacks.
💰 Cryptocurrency Clipper Feature
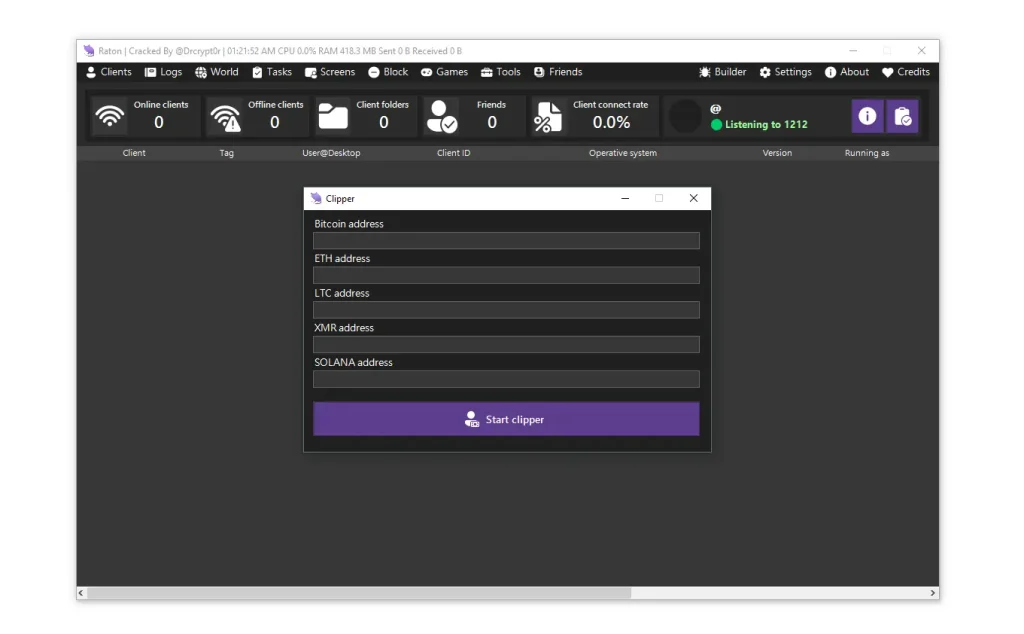
- 🔄 Clipboard Manipulation for Crypto:
This feature replaces copied cryptocurrency wallet addresses with attacker-controlled ones. Victims may unknowingly send funds to the wrong address. This type of attack is difficult to detect without careful verification. Users should always double-check wallet addresses before confirming transactions. Using secure wallets with verification features can reduce risk. This highlights the financial risk associated with RAT infections.
💸 Crypto Wallet Stealing
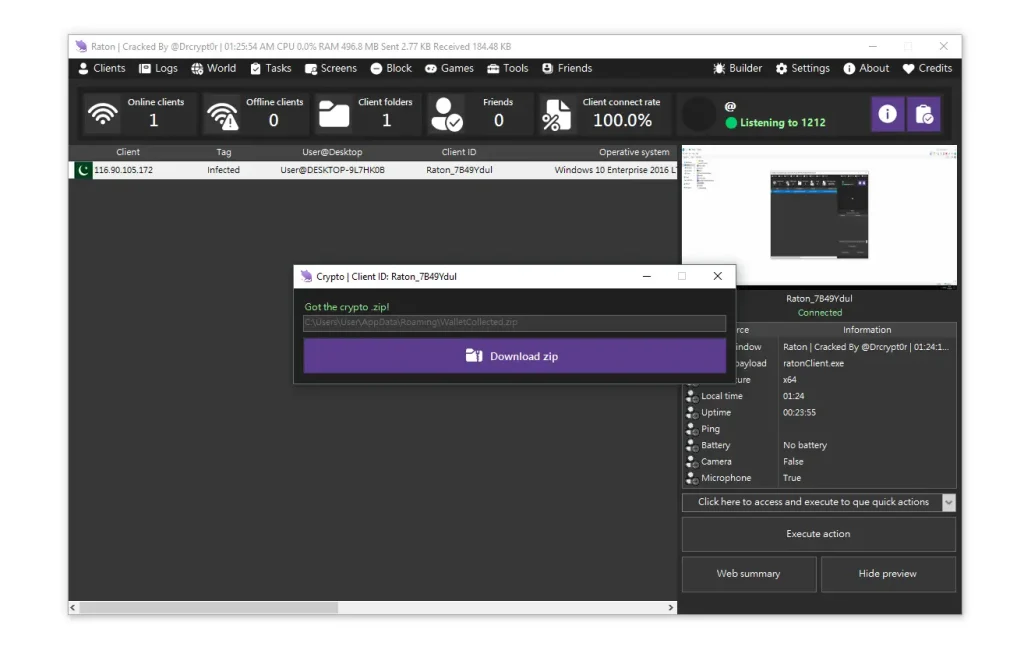
- 🧾 Wallet & Browser Data Extraction:
RATs can extract stored data from browsers and cryptocurrency wallets, including credentials and private keys. This data is often compressed and sent to attackers. Users should avoid storing sensitive information in browsers. Encrypting wallet data and using hardware wallets can provide additional protection. Regular monitoring of financial accounts is essential. This feature demonstrates the direct financial impact of malware.
🌐 DDOS Attack Feature
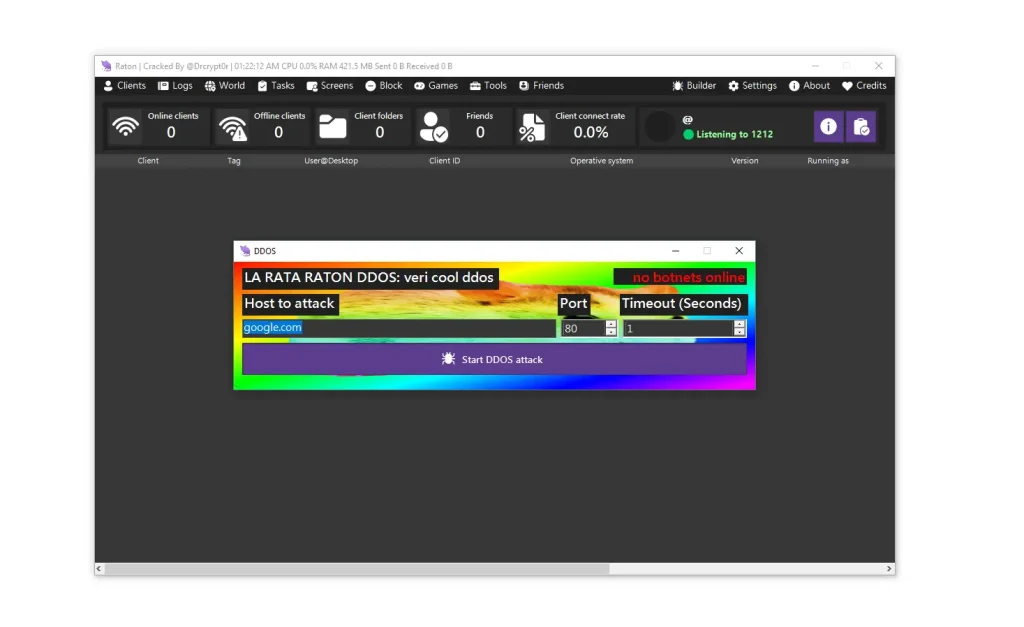
- 🌊 Botnet-Based Distributed Attacks:
Infected devices can be used to launch distributed denial-of-service attacks against websites or services. This can overwhelm servers and disrupt operations. Organizations should implement DDoS protection solutions and monitor traffic spikes. This feature highlights how compromised devices can be used in larger cyber operations.
🎭 Entertainment Features
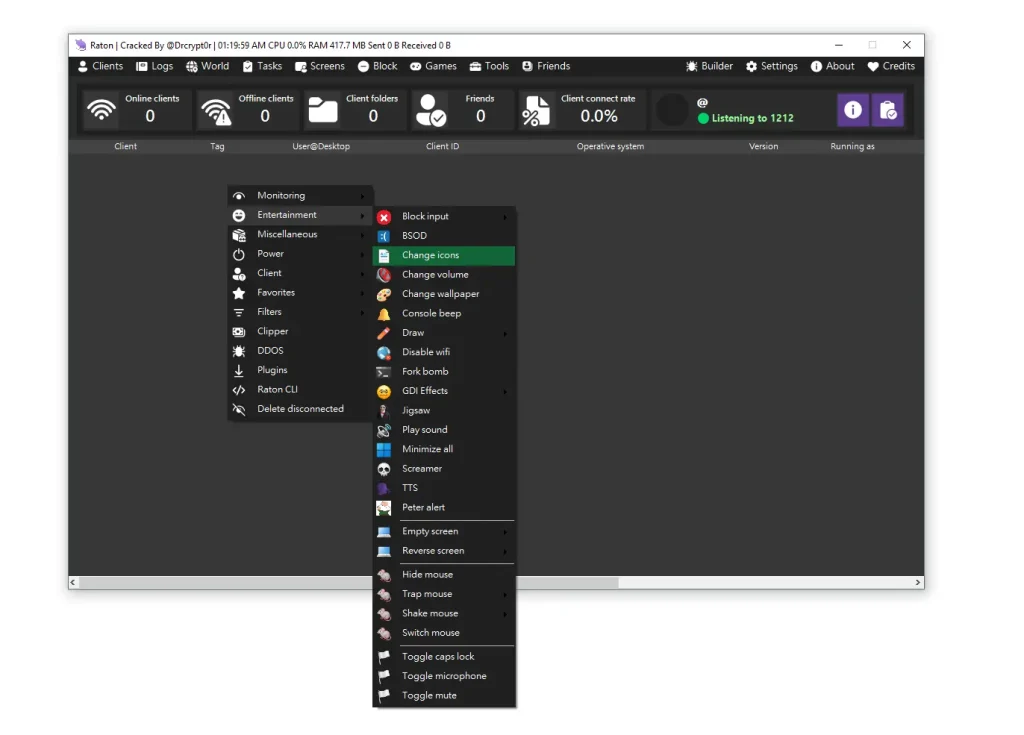
- 😈 User Disruption & Psychological Tactics:
These features include screen effects, sound playback, and input manipulation designed to confuse or intimidate users. While they may seem harmless, they indicate a deeper system compromise. Security awareness training can help users respond appropriately. This feature demonstrates the psychological aspect of cyberattacks.
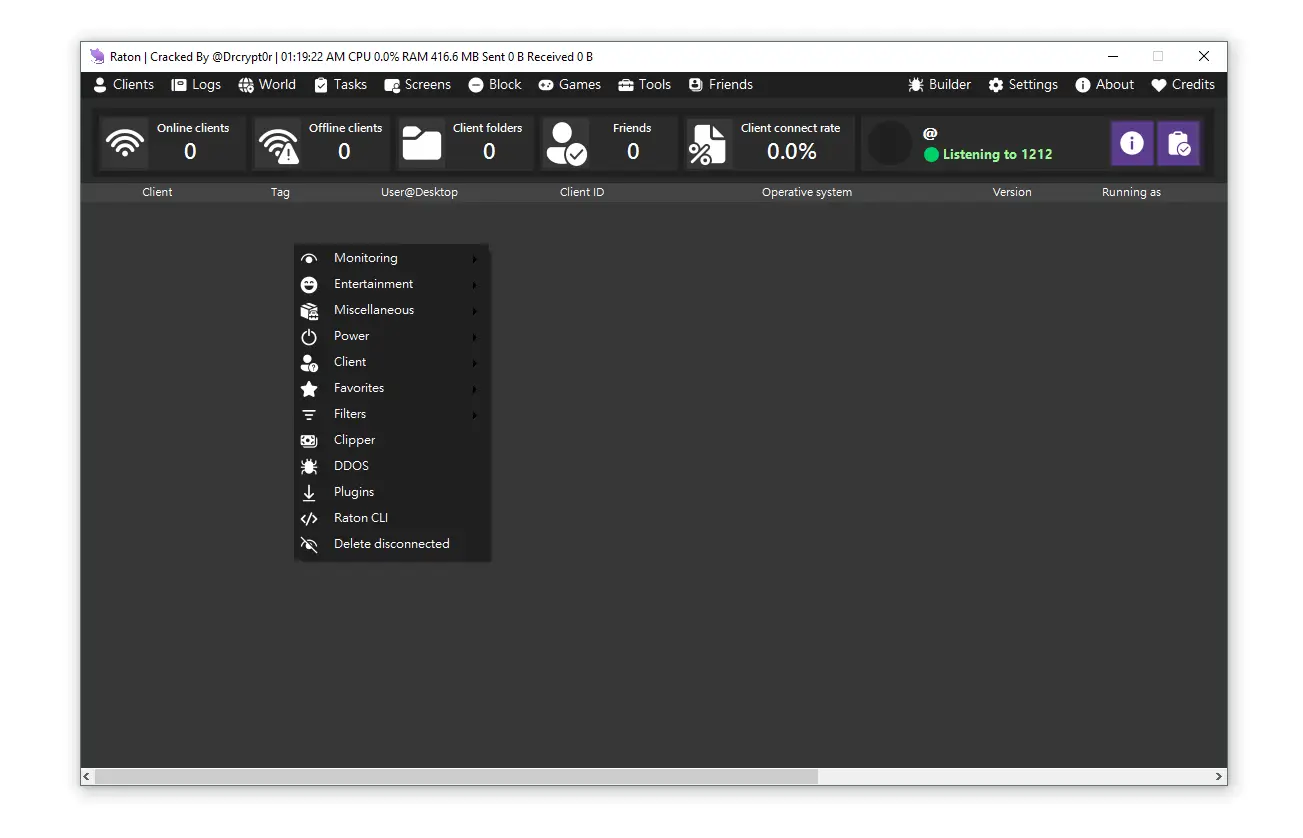
🖥️ Feature Image (Main UI)
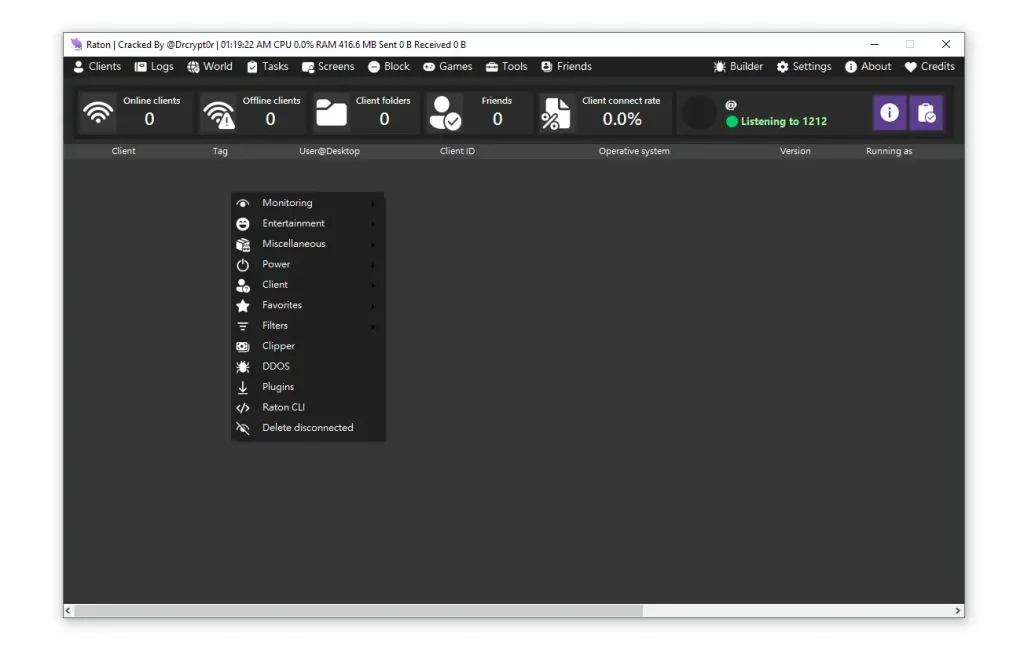
- 🧩 Centralized Interface Design:
The main interface provides access to all modules, allowing efficient management of infected systems. This highlights the organized nature of modern malware frameworks. Security professionals can study such interfaces to understand attacker workflows.
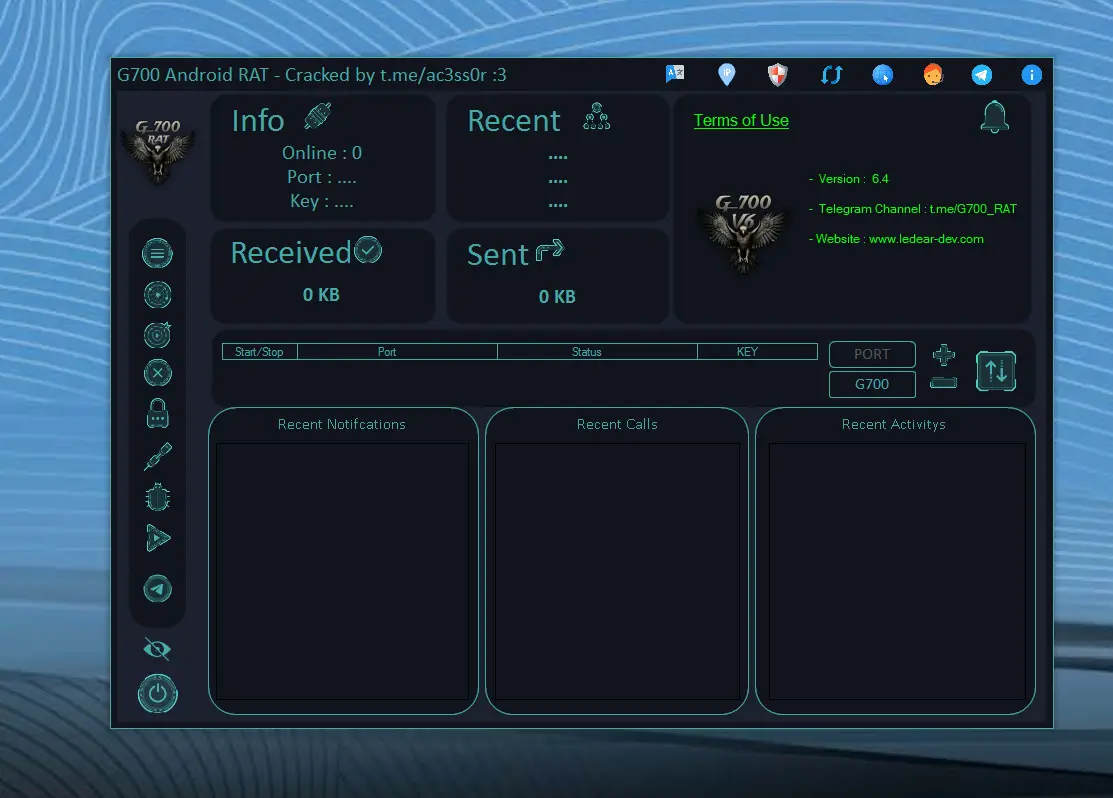
🖥️ HVNC Client Control
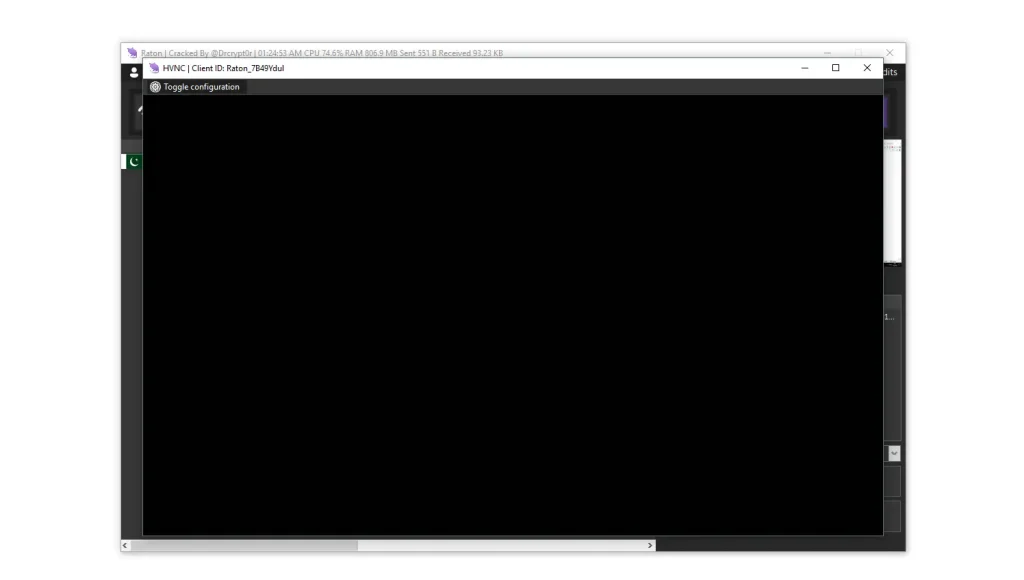
- 🕶️ Hidden Remote Desktop Access:
HVNC allows attackers to control a system without the user’s knowledge. This stealth capability makes detection extremely difficult. Monitoring unusual system behavior is essential. This feature highlights advanced surveillance techniques.
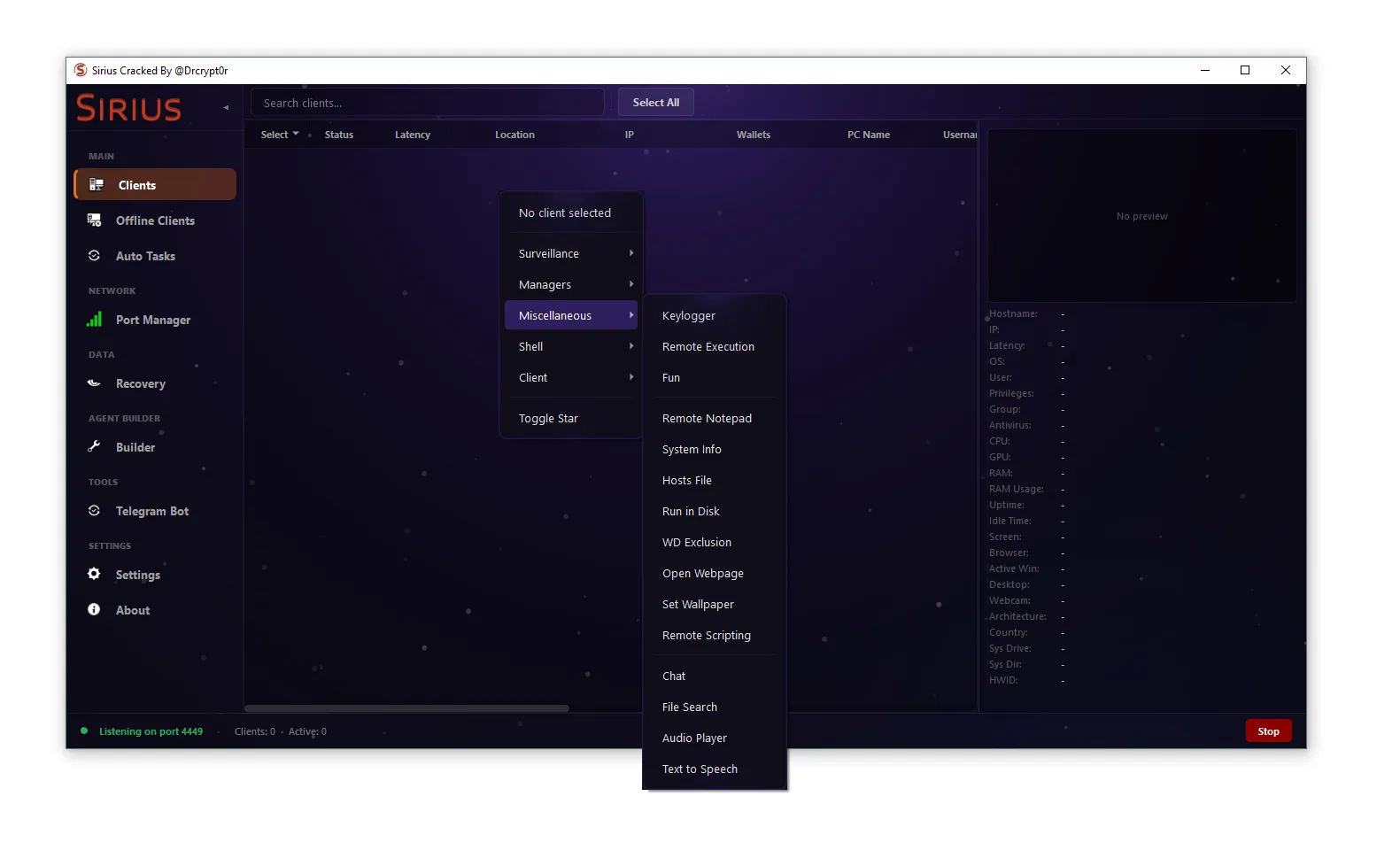
🧰 Miscellaneous Feature
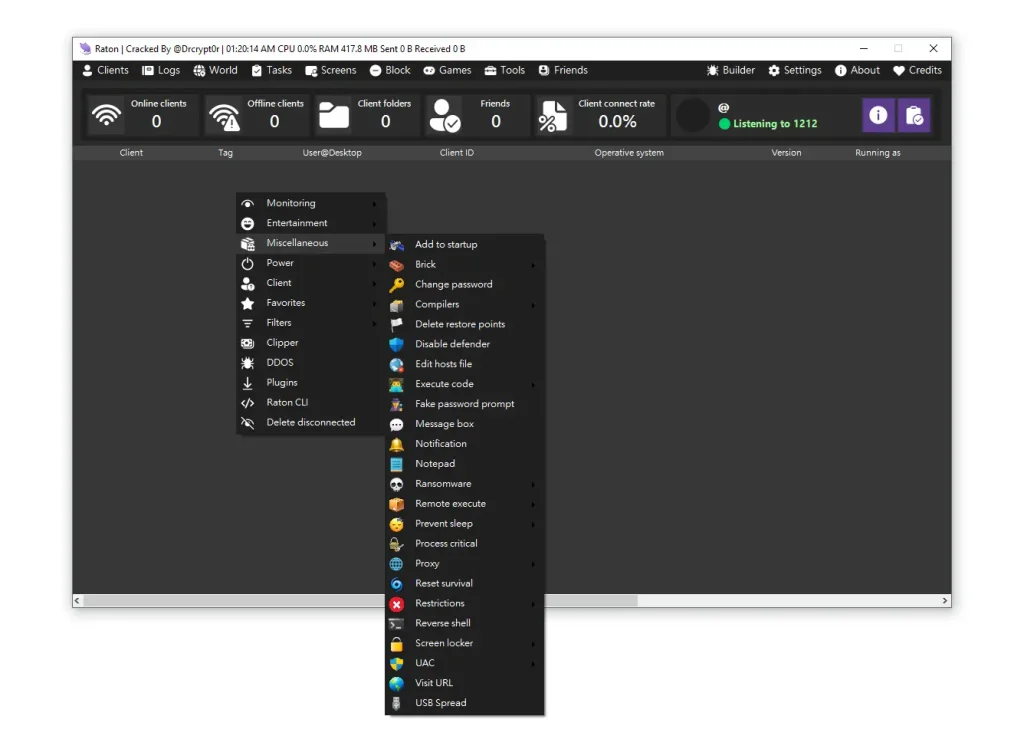
- 🧬 Advanced Post-Exploitation Tools:
This includes ransomware, reverse shell, and system modification capabilities. These tools allow attackers to expand their control and perform additional attacks. Organizations should implement layered security defenses. This feature demonstrates the versatility of modern RATs.
🎥 Monitoring Features
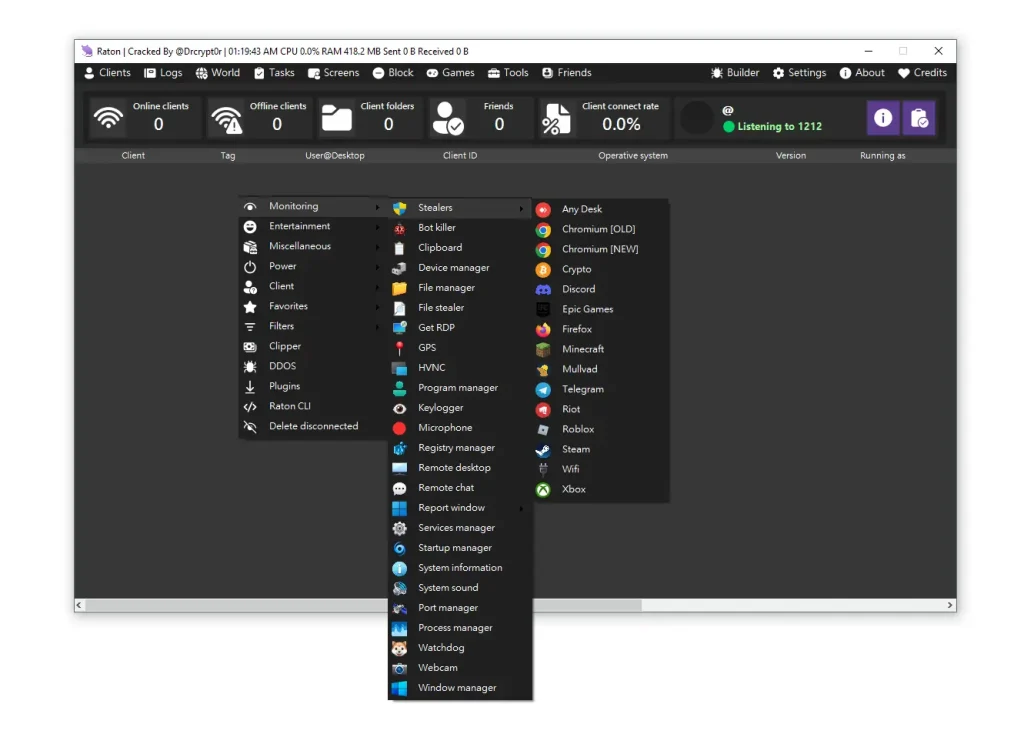
- 📸 Surveillance & Data Collection:
Includes webcam access, microphone recording, and keylogging. This allows attackers to monitor users in real time. Multi-factor authentication and monitoring tools can reduce risk. This feature highlights privacy concerns.
⚡ Power Control Feature
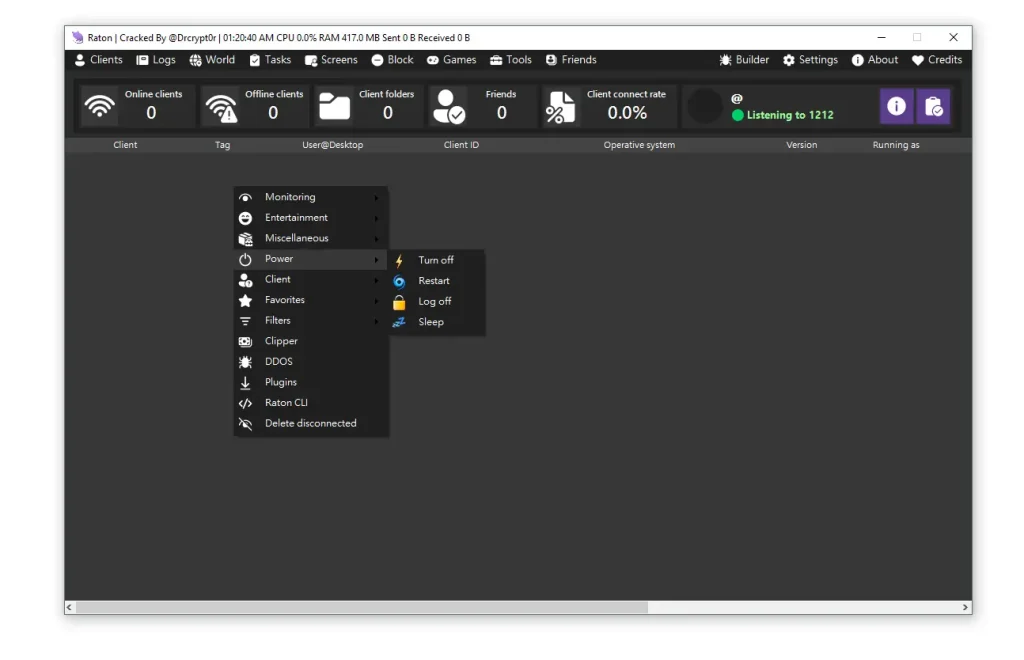
- 🔌 Remote Power Management:
Allows attackers to shut down or restart systems, disrupting operations. This can be particularly damaging in business environments. Monitoring system commands can help detect misuse.
🖥️ Remote Desktop
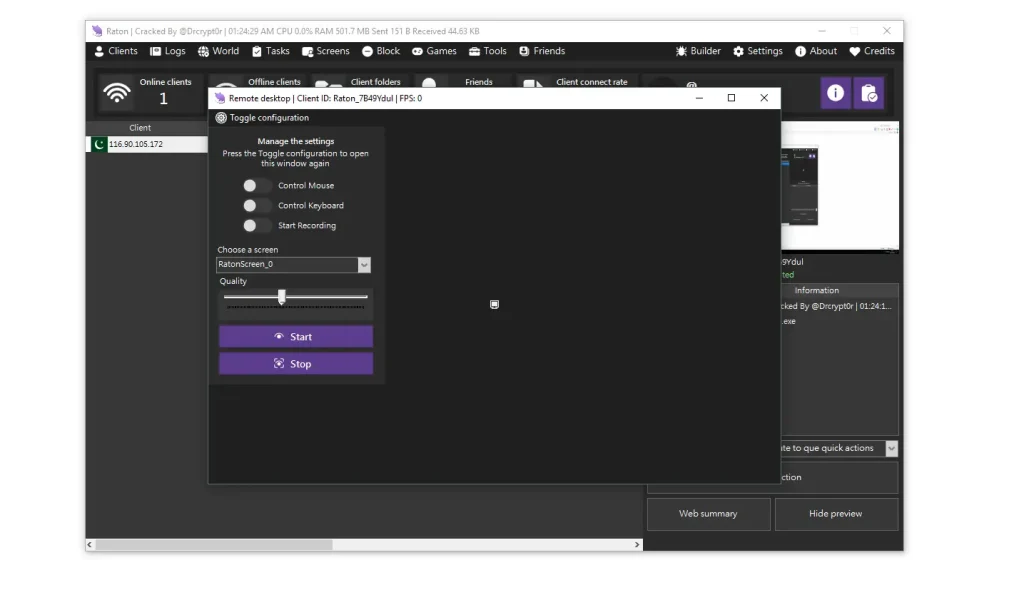
- 🖱️ Full System Interaction:
Provides complete control over the system, including mouse and keyboard input. This allows attackers to perform actions as if physically present. Strong access controls are essential.
🔍 Sorting Features
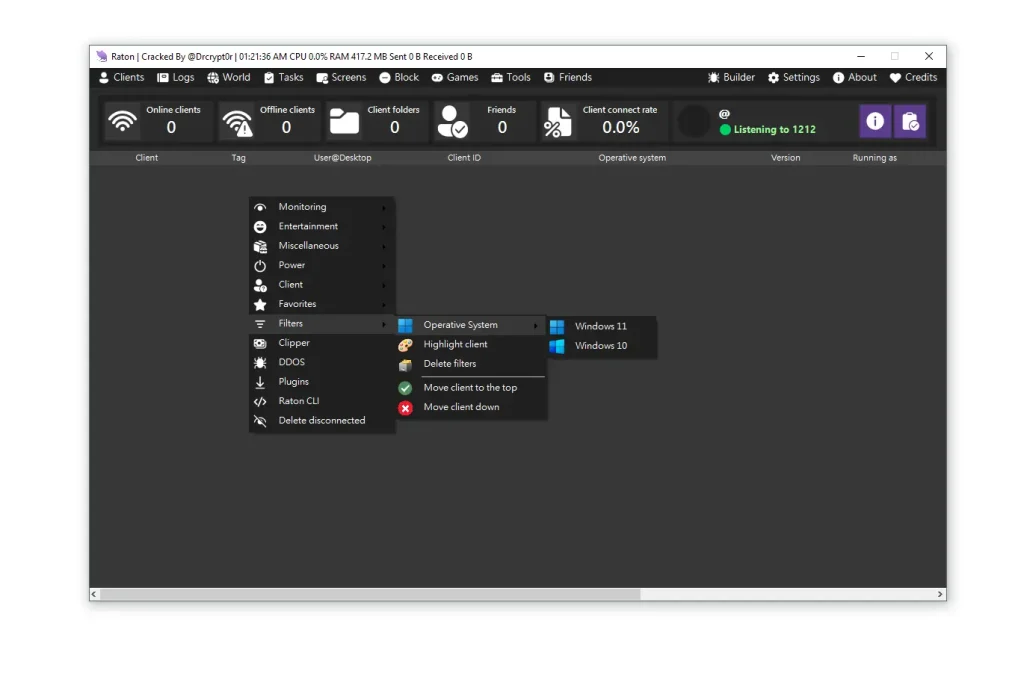
- 📊 Client Organization & Filtering:
Helps manage large numbers of infected systems efficiently. This demonstrates the scalability of modern cyber threats. Monitoring unusual patterns can aid detection.
Download Raton RAT 2026 Cracked
Virus Total Report of Raton RAT 2026 Cracked
https://www.virustotal.com/gui/file/9017749ca3bf56d30e657478655ef56d6a657575d02836420cc963a54144faff?nocache=1🏁 Final Verdict
Raton RAT 2026 Cracked is a highly advanced and multi-functional remote access threat that combines stealth, persistence, and powerful capabilities. Understanding its features is essential for building strong cybersecurity defenses.
By implementing advanced security measures, monitoring systems proactively, and educating users, organizations can significantly reduce their exposure to such threats.
❓ FAQs
❓ What is Raton RAT 2026 Cracked?
Raton RAT 2026 Cracked is an advanced remote access trojan used for system control, monitoring, and data theft.
❓ How does Raton RAT 2026 Cracked infect systems?
Through phishing emails, malicious downloads, and compromised software.
❓ Can Raton RAT 2026 Cracked be detected?
Yes, with advanced behavior-based security tools and monitoring systems.
❓ What are the main risks?
Data theft, financial loss, privacy invasion, and system compromise.
❓ How to protect against RATs?
Use updated security software, enable multi-factor authentication, and avoid suspicious files.
❓ Is Raton RAT 2026 Cracked legal?
Only for authorized testing in controlled environments.
❓ What should I do if infected?
Disconnect from the network, run a full scan, and seek professional help.