The digital landscape in 2026 has become increasingly complex, with cyber threats evolving at a rapid pace. Among the most dangerous categories of malware is the Remote Access Trojan (RAT), a tool designed to give attackers full control over infected systems.
One of the most advanced examples in this category is Anti Globalization RAT V 2026, a sophisticated malware framework capable of surveillance, system manipulation, data theft, and network exploitation.
Unlike traditional viruses, RATs operate silently in the background, making them extremely difficult to detect without proper cybersecurity measures.
⚙️ What is Anti Globalization RAT V 2026?
Anti Globalization RAT V 2026 is a malicious remote administration tool designed to allow unauthorized access to a computer system over a network.
🛑 Core Functionality:
- Remote system control
- Data extraction and surveillance
- File manipulation
- Network exploitation
- Botnet coordination
This type of malware is often used in cybercrime operations, targeting individuals, businesses, and even enterprise-level systems.
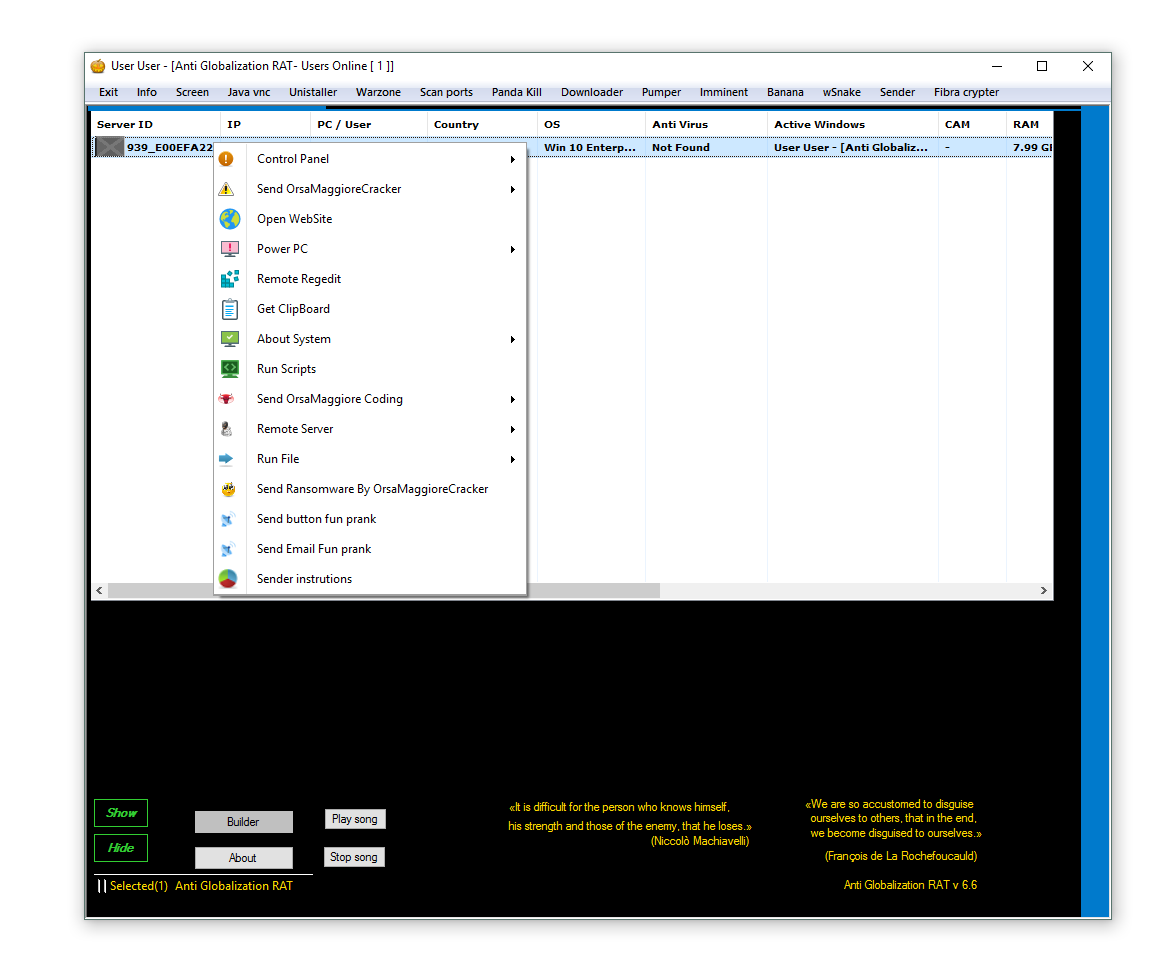
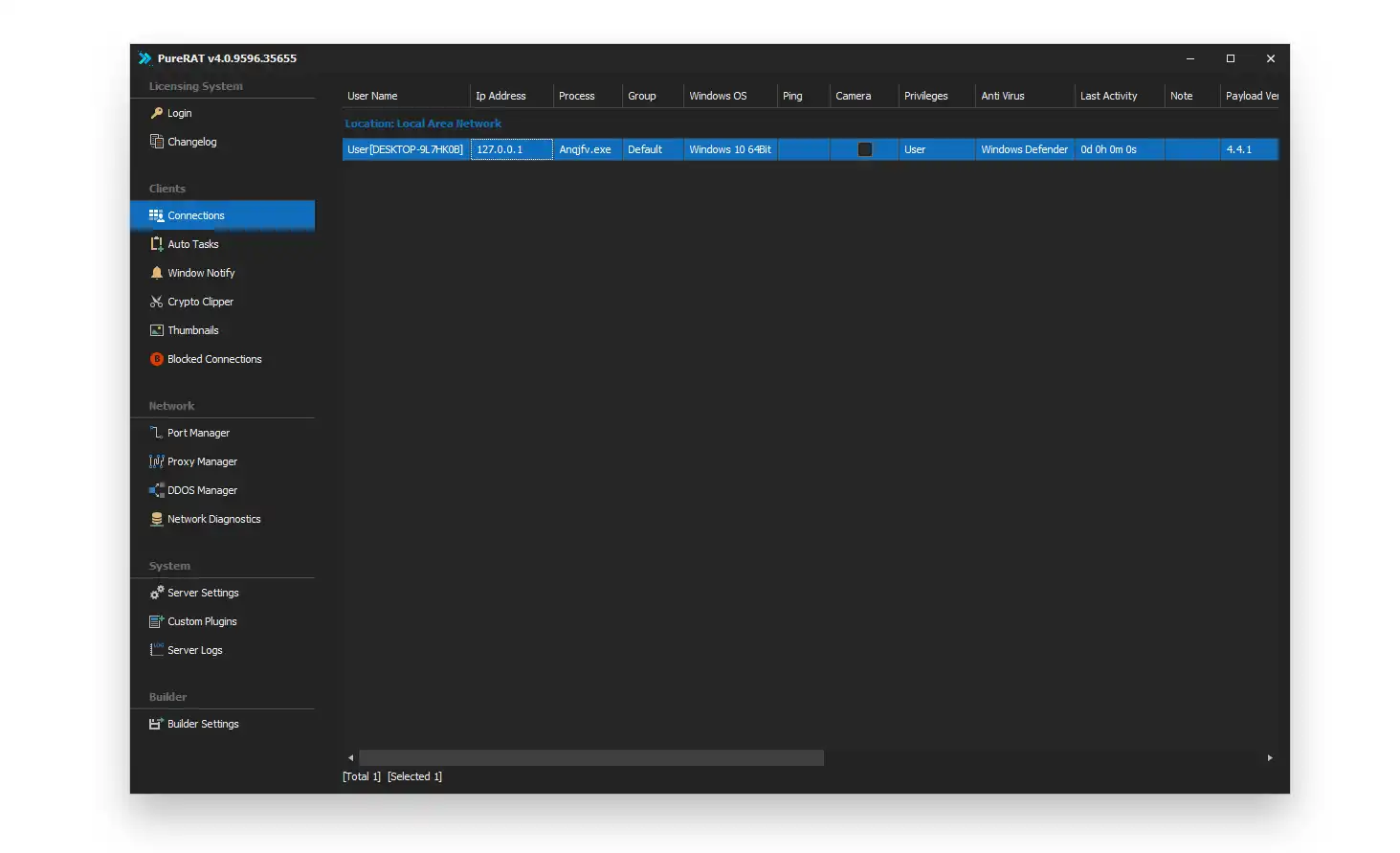
🖥️ Control Panel System – The Attack Command Center
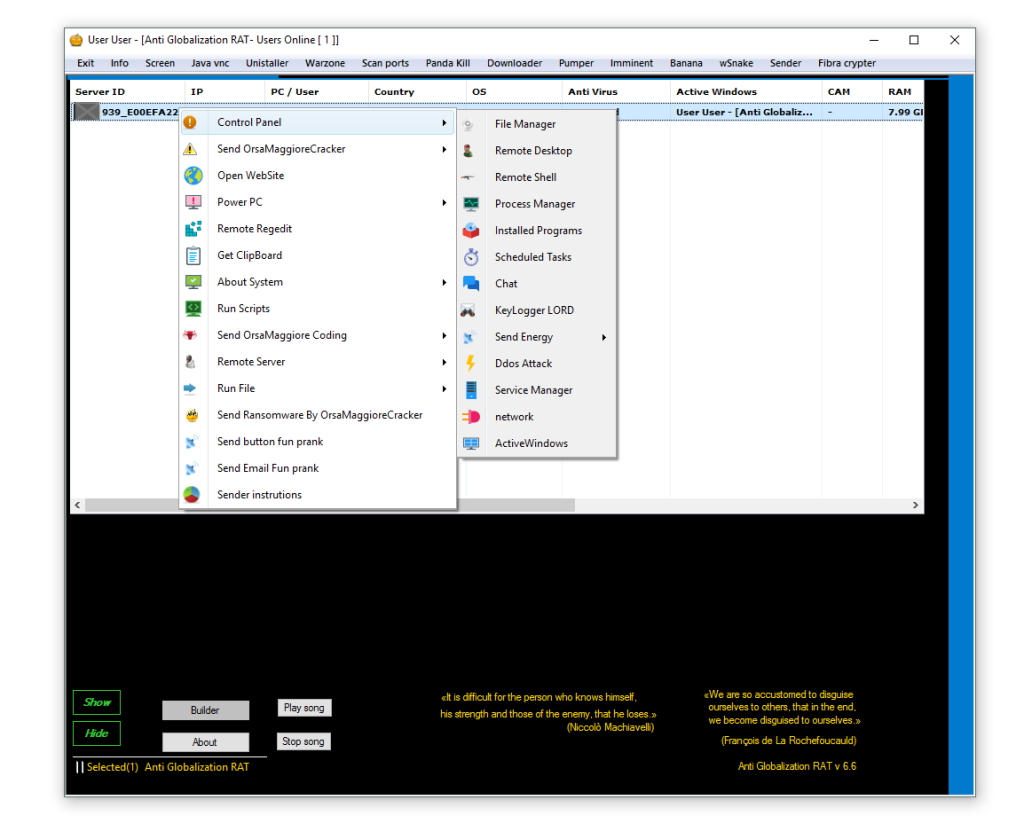
The control panel is the central hub of the RAT, allowing attackers to manage infected systems remotely.
🔹 Multi-System Management:
Attackers can control multiple infected devices simultaneously. This scalability makes it extremely dangerous for large-scale cyberattacks.
🔹 Real-Time Monitoring:
The dashboard provides live updates of system status, user activity, and connection logs, enabling continuous surveillance.
🔹 Stealth Communication:
The control panel communicates with infected systems using encrypted or hidden channels, making detection difficult for standard antivirus tools.
🔹 Operational Efficiency:
Even low-skilled attackers can operate complex cyberattacks due to the simplified interface.
📁 File Manager – Full Data Control & Theft System
The file manager module allows complete access to a victim’s file system.
🔹 Remote File Access:
Attackers can browse, open, download, or delete files on the infected system.
🔹 Sensitive Data Extraction:
Important documents such as:
- Financial records
- Business reports
- Personal images
- Password files
can be silently stolen.
🔹 System Corruption Capability:
Attackers can modify system files, potentially causing system instability or permanent damage.
🔹 Long-Term Espionage:
Continuous file access enables ongoing surveillance of sensitive data.
🖥️ Remote Desktop (VNC / Java VNC) – Full Visual Control
This feature provides real-time screen access to the victim’s device.
🔹 Live Screen Viewing:
Attackers can see everything happening on the screen in real time.
🔹 Input Control:
Keyboard and mouse inputs can be fully controlled remotely.
🔹 Behavioral Tracking:
Every action such as browsing, typing, and login attempts can be monitored.
🔹 Invisible Surveillance:
The user often has no indication that their screen is being watched.
💻 Remote Shell Access – Advanced System Manipulation
Remote shell access provides command-line control over the system.
🔹 System Command Execution:
Attackers can run system-level commands using CMD or PowerShell.
🔹 Administrative Control:
This includes installing software, changing settings, or modifying security policies.
🔹 Stealth Execution:
Commands can run silently without visible windows or alerts.
🔹 Deep System Access:
This is one of the most powerful features for full system compromise.
🔑 Keylogger Module – Credential Theft Engine
The keylogger is one of the most dangerous components.
🔹 Keystroke Recording:
Every keyboard input is recorded in real time.
🔹 Password Theft:
Login credentials for banking, email, and social media accounts can be captured.
🔹 Behavioral Intelligence:
Long-term logging allows attackers to build detailed user profiles.
🔹 Silent Operation:
Keylogging runs invisibly without user awareness.
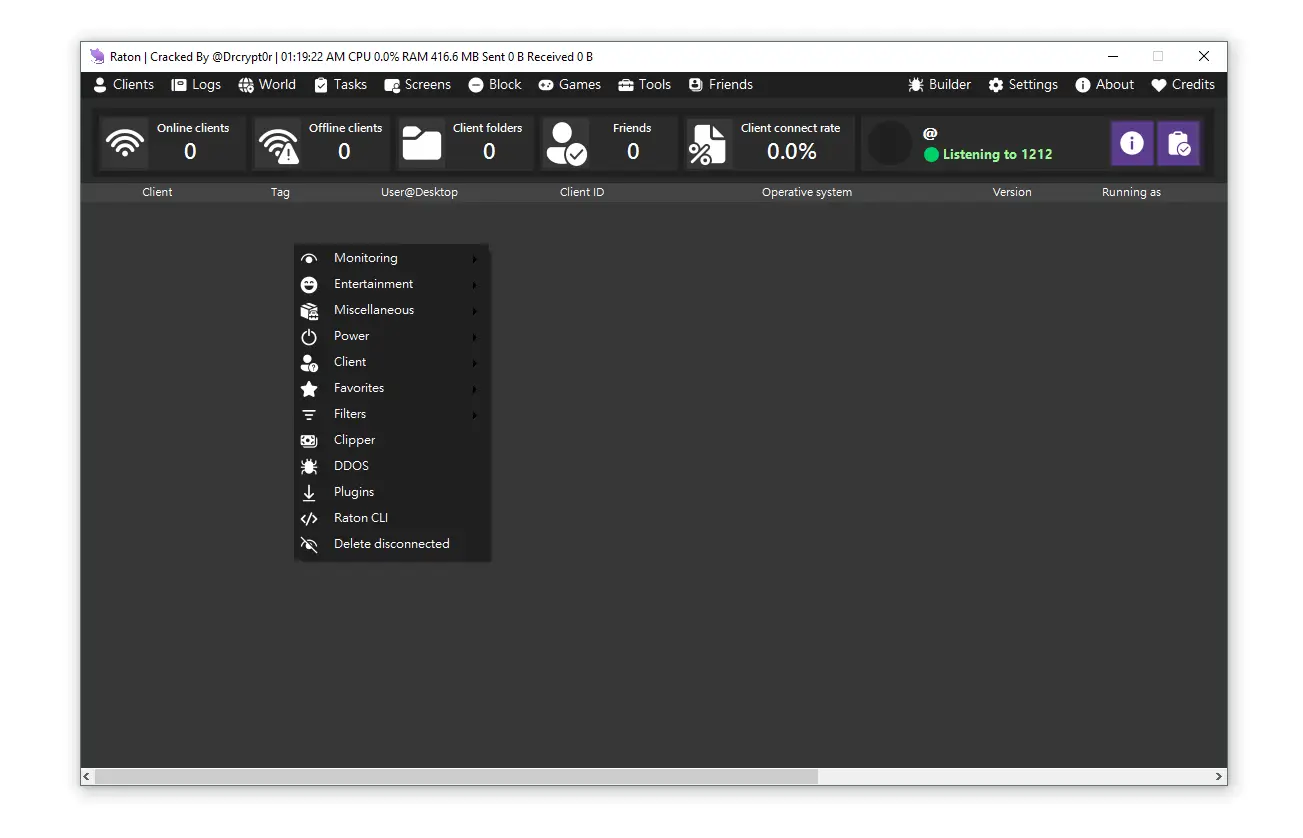
🌐 Network Attack & DDoS Capability – Botnet Warfare
This module enables large-scale network attacks.
🔹 Distributed Attacks:
Multiple infected systems are used to overwhelm servers or websites.
🔹 Botnet Formation:
Infected devices are linked together into a coordinated attack network.
🔹 Network Scanning:
Attackers identify vulnerabilities in connected systems.
🔹 Infrastructure Damage:
Websites and online services can be disrupted or taken offline.
🧾 Process Manager – System Control Override
🔹 Process Manipulation:
Attackers can start or stop system processes remotely.
🔹 Security Disabling:
Antivirus and firewall processes can be terminated.
🔹 Resource Hijacking:
System performance can be intentionally degraded.
🔹 Stability Risks:
Improper process handling may crash the system.
🔧 Service Manager – Persistence & Control
🔹 Background Service Control:
System services can be modified or disabled.
🔹 Auto-Start Persistence:
Malware can ensure it runs at every system startup.
🔹 Long-Term Infection:
This allows persistent access over long periods.
🔹 System Disruption:
Critical services may be disabled.
📋 Clipboard Monitoring – Silent Data Capture
🔹 Copy Data Theft:
Anything copied by the user can be intercepted.
🔹 Financial Exposure:
Credit card numbers and sensitive data are at risk.
🔹 Invisible Tracking:
Users remain unaware of clipboard monitoring.
🔹 High Risk for Online Transactions:
Banking and payment data are especially vulnerable.
⚡ System Power Control – User Disruption Tools
🔹 Remote Shutdown:
Attackers can turn off the system remotely.
🔹 Forced Restart:
Interrupts ongoing tasks or workflows.
🔹 System Freeze:
Locks system interaction completely.
🔹 Operational Damage:
Can cause business downtime and productivity loss.
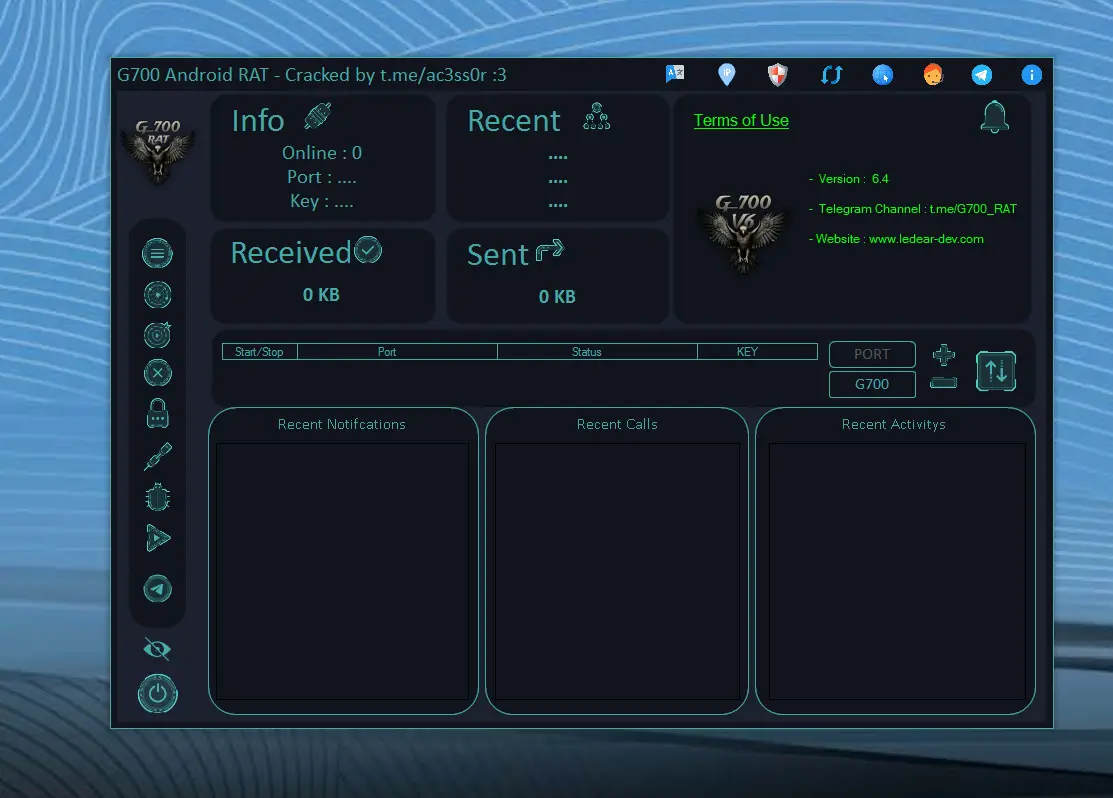
💣 Ransomware Module – Data Encryption Attack
🔹 File Locking:
User files are encrypted and made inaccessible.
🔹 Ransom Demand:
Victims are forced to pay to regain access.
🔹 Permanent Data Loss Risk:
Improper recovery can lead to irreversible damage.
🔹 High Financial Impact:
Commonly used in corporate cyberattacks.
🌍 Browser Control & Social Engineering
🔹 Forced Website Redirection:
Users can be redirected to malicious websites.
🔹 Phishing Attacks:
Fake login pages are used to steal credentials.
🔹 Psychological Manipulation:
Users can be tricked into unsafe actions.
🔹 Data Harvesting:
Sensitive input through fake pages is captured.
📊 System Information & IP Tracking
🔹 Device Profiling:
Full hardware and software details are collected.
🔹 IP Address Tracking:
Both internal and external IP addresses are captured.
🔹 Target Identification:
Helps attackers categorize victims.
🔹 Attack Optimization:
Data is used for targeted exploitation.
⚠️ Global Cybersecurity Risks
Anti Globalization RAT V 2026 represents serious threats:
- Identity theft
- Corporate espionage
- Financial fraud
- Data breaches
- GDPR compliance violations
- Botnet-based cyber warfare
🛡️ How to Protect Against RAT Malware
🔹 Use Advanced Security Software:
Enterprise-grade antivirus and endpoint protection.
🔹 Avoid Untrusted Downloads:
Do not install cracked or unknown software.
🔹 Enable Firewalls:
Monitor incoming and outgoing traffic.
🔹 Keep Systems Updated:
Patch vulnerabilities regularly.
🔹 Enable Multi-Factor Authentication:
Protect sensitive accounts.
Download Anti Globalization RAT V 2026
Virus Total Report
https://www.virustotal.com/gui/file/bdac2363537f3f5de692ba498070d7a265d74544c645548c7b3dcd613e22c0bb📌 Conclusion
Anti Globalization RAT V 2026 is a highly advanced malware system that demonstrates how modern cyber threats combine surveillance, system control, and attack capabilities into a single framework.
Understanding its structure is essential for individuals, businesses, and cybersecurity professionals aiming to protect digital infrastructure in 2026 and beyond.
❓ Frequently Asked Questions (FAQs) about Globalization RAT V 2026
❓ What is Anti Globalization RAT V 2026?
It is a Remote Access Trojan that allows attackers to remotely control infected systems.
❓ Is RAT malware illegal?
Yes, unauthorized use is illegal in the United States, Europe, and most countries worldwide.
❓ How does RAT infect systems?
Through phishing emails, malicious downloads, and cracked software.
❓ Can antivirus detect RAT malware?
Yes, but advanced RATs may bypass basic detection methods.
❓ What is the biggest risk of RAT infection?
Full system compromise, identity theft, and financial data theft.