Pentest tools
TDork – (DorkGen & Scanner)
TDork – (DorkGen & Scanner)
SQLi Dorks Generator v0.2
SQLi Dorks Generator v0.2
Acunetix Web Vulnerability Scanner 12.0.19051514 Full Crack
Acunetix Web Vulnerability Scanner 12.0.19051514 Full Crack Acunetix Web Interface Acunetix ships with an easy to use web interface, allowing multiple users to use...
Acunetix Web Vulnerability Scanner v13.0.200217097 for Linux x64
Acunetix Web Vulnerability Scanner v13.0.200217097 for Linux x64 In today’s digital landscape, web applications are the backbone of countless businesses. They handle sensitive data,...
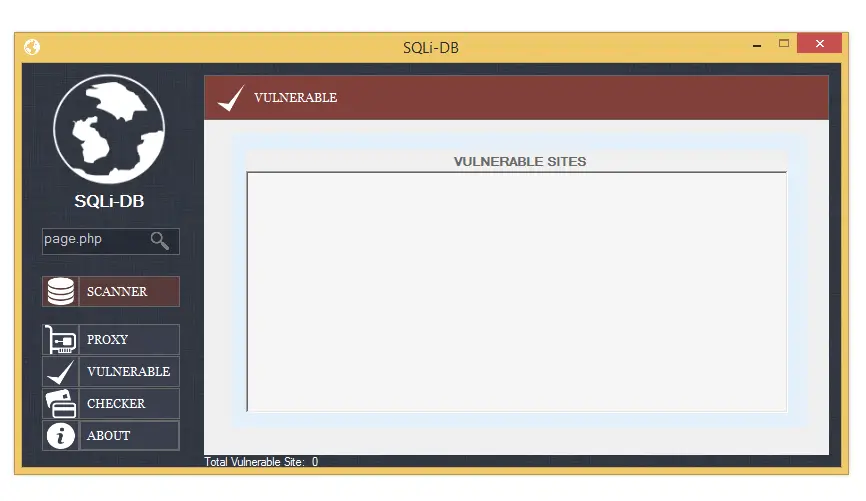
SQLi-DB-SQL Injection Dork Scanner v1.0
SQLi-DB-SQL Injection Dork Scanner v1.0
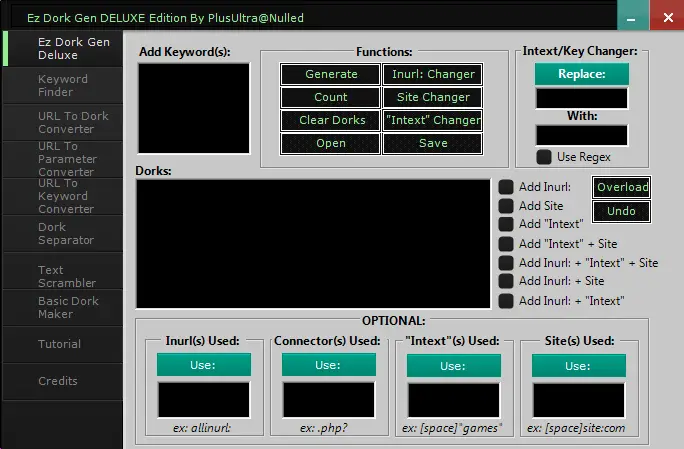
Ez Dork Gen DELUXE Edition 2024
Ez Dork Gen DELUXE Edition 2024 The internet is a vast ocean of information, but beneath the surface lies a hidden layer, accessible through...
SQLi Dork Scanner with Dork list 2024
SQLi Dork Scanner with Dork list 2024 The world of web security is a constant battle between defenders and attackers. One tool sometimes used...
SQLi Dumper 9.7
SQLi Dumper 9.7 SQLi Dumper v.9.7 – database dump harvester. Finds and promotes sql and XSS vulnerabilities on vulnerable sites and outputs ready-made email...