Introduction: What is QZK RAT 2026?
QZK RAT 2026 is a modern modular Remote Access Trojan (RAT) framework designed to combine multiple cybercrime capabilities into a single malware management platform. Unlike older malware families that focused on only one attack technique, QZK RAT 2026 integrates remote access, credential theft, ransomware deployment, cryptocurrency mining, clipboard hijacking, and persistence features into one centralized interface.
Security researchers have observed that malware frameworks like QZK RAT 2026 are becoming increasingly dangerous because they lower the barrier to entry for cybercriminals. Attackers no longer need advanced programming skills to launch sophisticated attacks against businesses, organizations, or individual users.
This article provides a detailed cybersecurity-focused analysis of the leaked QZK RAT 2026 interface, its modules, attack capabilities, persistence methods, and defensive considerations for security teams.
🔹 1. QZK Binder
The QZK Binder module inside QZK RAT 2026 is designed to combine malicious payloads with legitimate-looking files. This technique helps malware operators disguise infected files as harmless applications, documents, or installers.
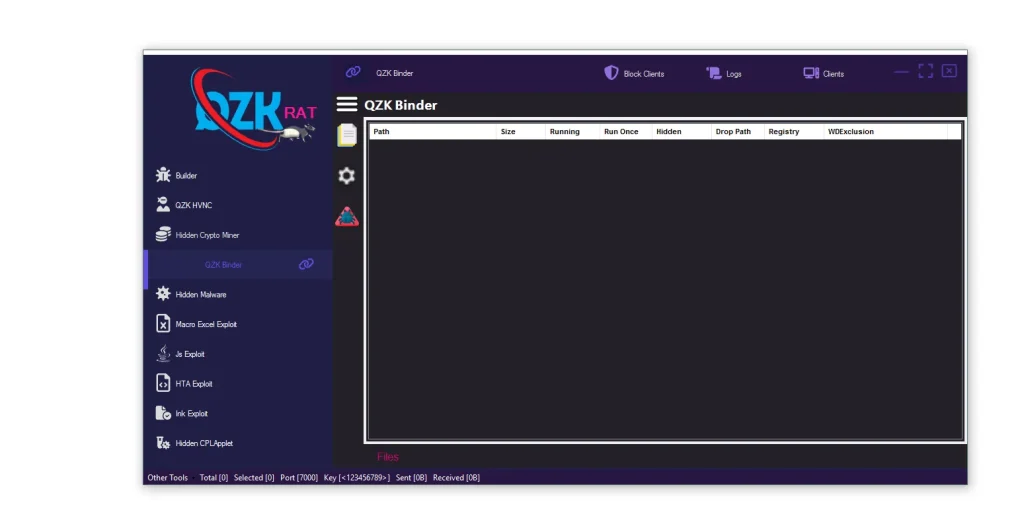
⚙️ Features displayed in QZK RAT 2026:
- 🧩 Block Clients / Logs / Clients: These management sections allow attackers to organize infected systems, review activity logs, and track malware deployment campaigns. Centralized monitoring improves operational control over compromised machines.
- 📂 Path: The path configuration determines where malware components are placed inside the Windows operating system. Threat actors often use common folders to reduce suspicion and blend with normal system activity.
- 📏 Size: File size customization helps malicious executables appear similar to legitimate software. Matching expected file sizes can reduce suspicion among victims and bypass simple security checks.
- ▶️ Running: This execution setting controls how and when the payload launches. Attackers use delayed execution or silent background launching to avoid immediate detection.
- 🔁 Run Once: The Run Once option ensures the malware executes a single time during installation. This behavior minimizes repeated alerts and reduces the chance of drawing user attention.
- 👁️ Hidden: Hidden execution allows the malicious process to run silently in the background without visible windows or notifications. Stealth techniques like this are common in modern RAT frameworks.
- 📁 Drop Path: This setting defines where extracted components are stored after execution. Malware frequently uses temporary folders or hidden directories for persistence.
- 🛡️ Registry: Registry persistence enables malware to automatically relaunch after system reboot. Attackers commonly abuse Windows startup keys for long-term access.
- 🚫 WIDExclusion: Exclusion settings may prevent infections on certain systems, regions, or security environments. Threat actors often avoid analysis systems and sandbox environments.
⚠️ Threat Level in QZK RAT 2026:
High – The binder module improves stealth and increases the likelihood of successful malware execution.
🔹 2. Hidden Crypto Miner
The Hidden Crypto Miner module in QZK RAT 2026 focuses on unauthorized cryptocurrency mining using victim hardware resources. These miners silently consume CPU and GPU power to generate cryptocurrency revenue for attackers.
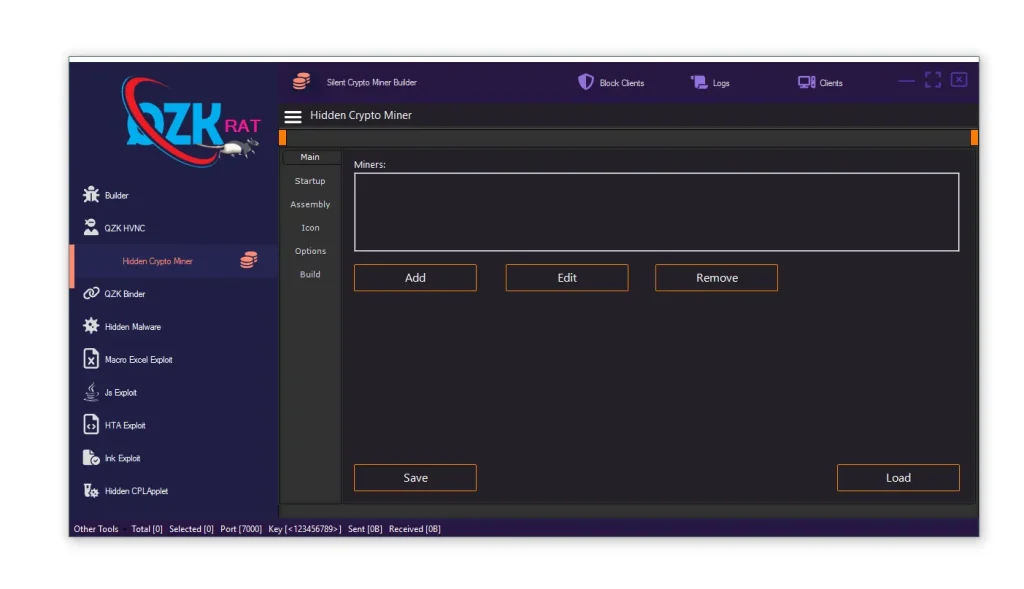
⚙️ Features displayed in QZK RAT 2026:
- ⛏️ Main: The main configuration panel controls core mining behavior including resource usage, mining intensity, and operational settings.
- 📋 Miners: This section manages multiple miner profiles and deployment options. Attackers can customize different miner variants for different targets.
- 🚀 Startup: Startup persistence ensures the miner launches automatically when Windows boots. Persistent miners can remain active for long periods without user awareness.
- 🧬 Assembly: Assembly customization changes malware metadata and binary signatures. These modifications are commonly used to evade traditional antivirus detection.
- 🖼️ Icon: Icon spoofing allows malicious files to mimic trusted applications or Windows system tools. Visual deception increases the success rate of malware delivery.
- ⚙️ Options: Resource management settings help reduce CPU spikes and overheating. Limiting resource consumption helps malware avoid detection by users.
- 🏗️ Build: The build process compiles the final malware payload. Attackers can generate customized variants for specific campaigns.
- 💾 Save / Load: Configuration saving enables threat actors to reuse malware settings across multiple attacks or deployment waves.
⚠️ Threat Level in QZK RAT 2026:
Critical – Hidden mining operations can damage hardware, increase electricity costs, and reduce enterprise system performance.
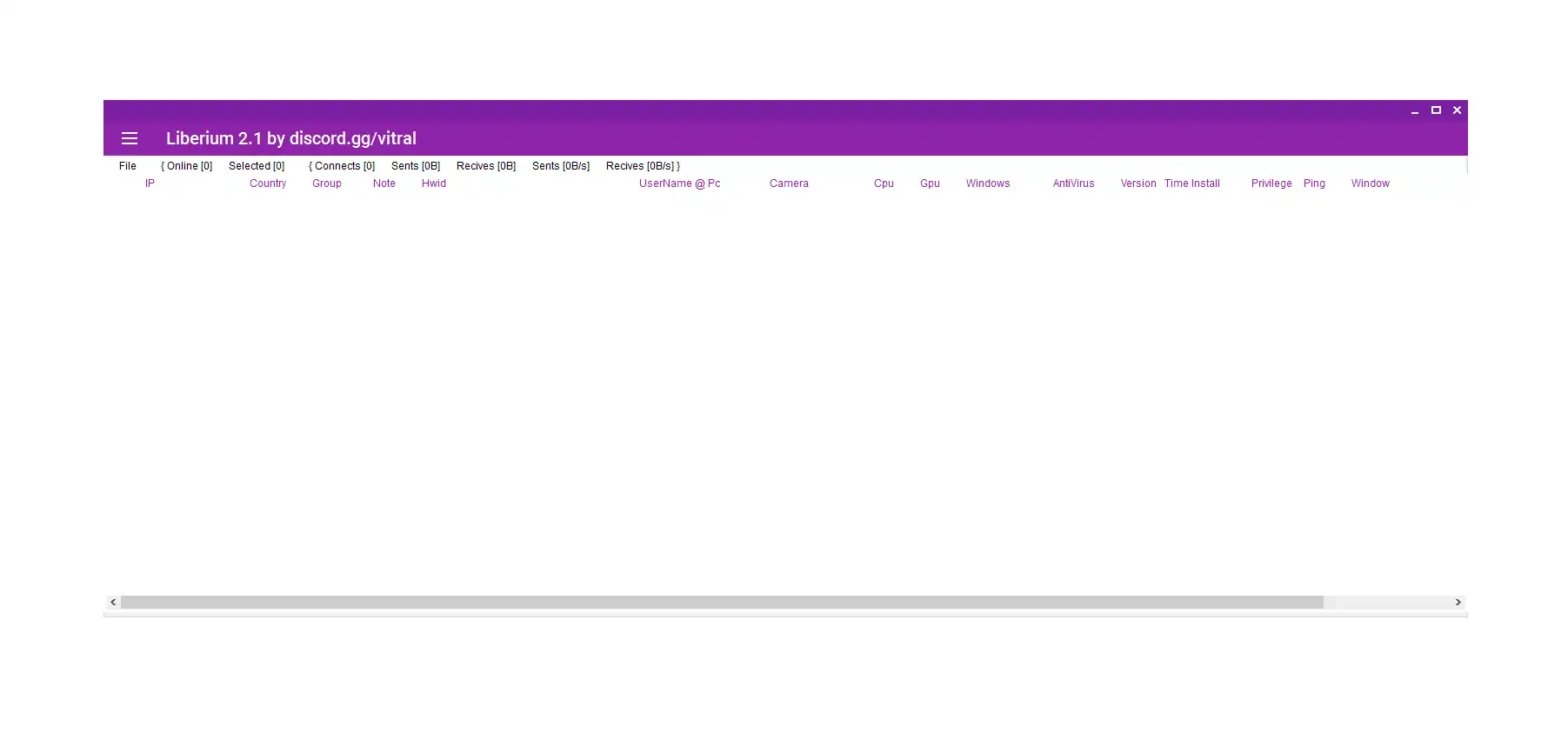
🔹 3. ZKRAT – Crypto Clipper
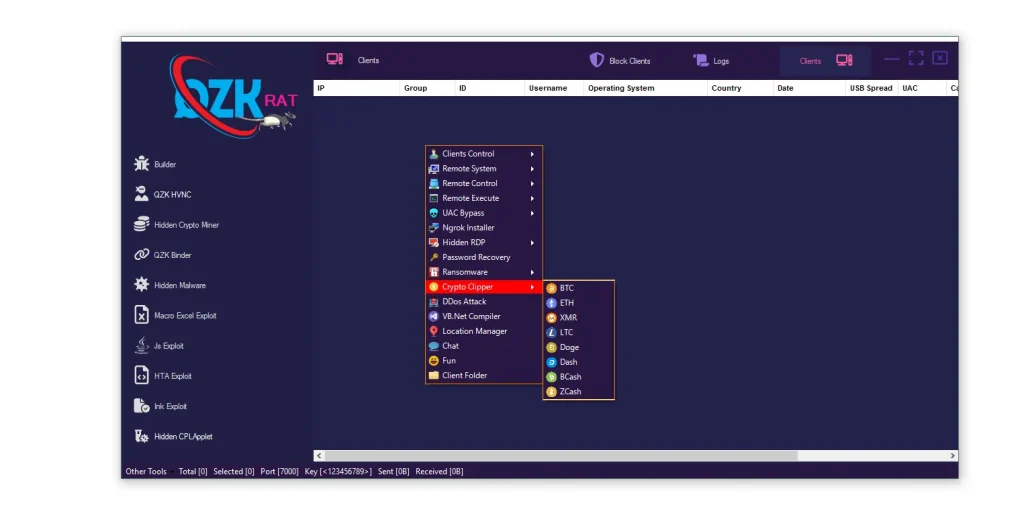
The Crypto Clipper module in QZK RAT 2026 is designed to hijack cryptocurrency transactions by monitoring clipboard activity and replacing copied wallet addresses.
⚙️ Features displayed in QZK RAT 2026:
- 💻 Clients: The infected client dashboard displays detailed information about compromised systems including operating system, geographic region, and infection status.
- 🪙 BTC, ETH, XMR, LTC, Doge, Dash, BCash, ZCash: Support for multiple cryptocurrencies increases monetization opportunities for attackers. Multi-wallet support makes the malware more versatile.
- 🕹️ Clients Control: The centralized management panel gives operators remote control capabilities including surveillance, payload deployment, and credential theft.
⚠️ Threat Level in QZK RAT 2026:
Critical – Victims may lose cryptocurrency funds instantly without realizing their clipboard data was modified.
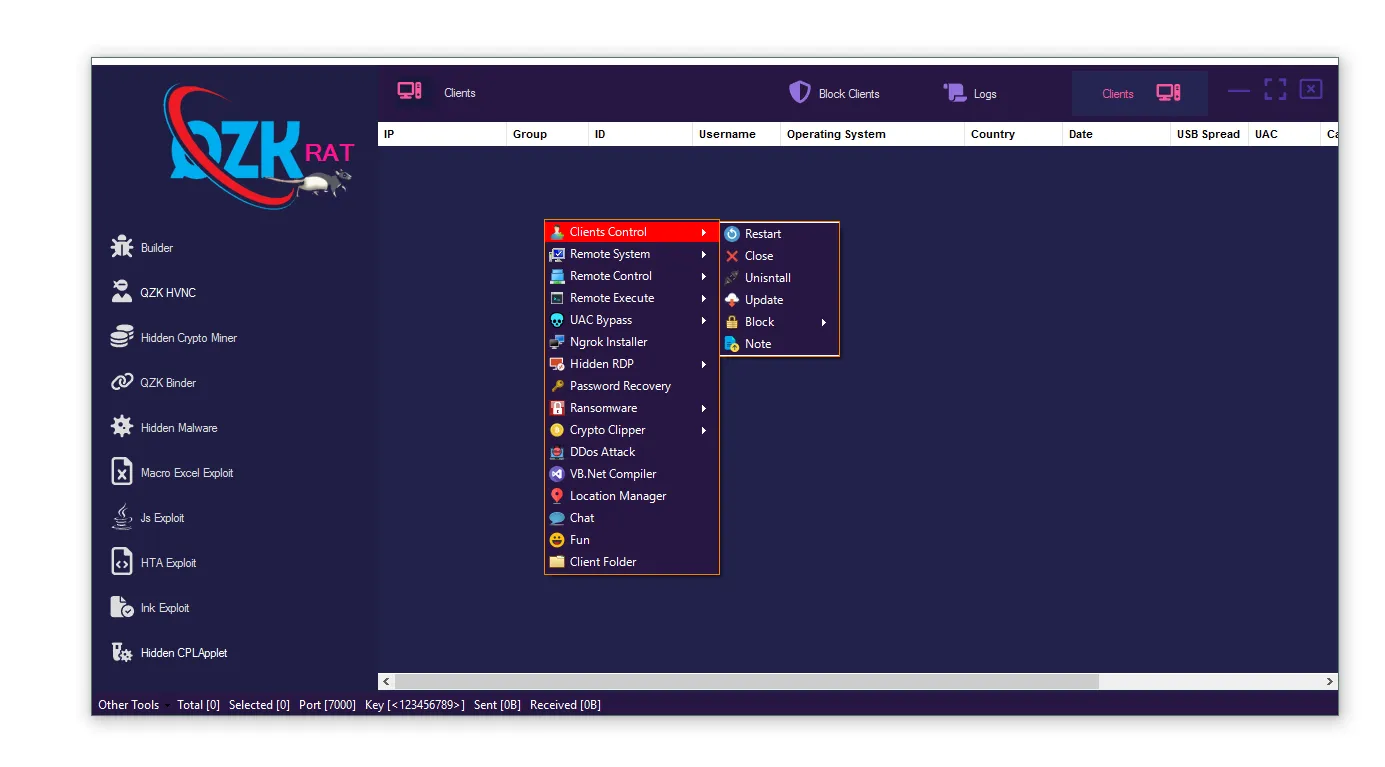
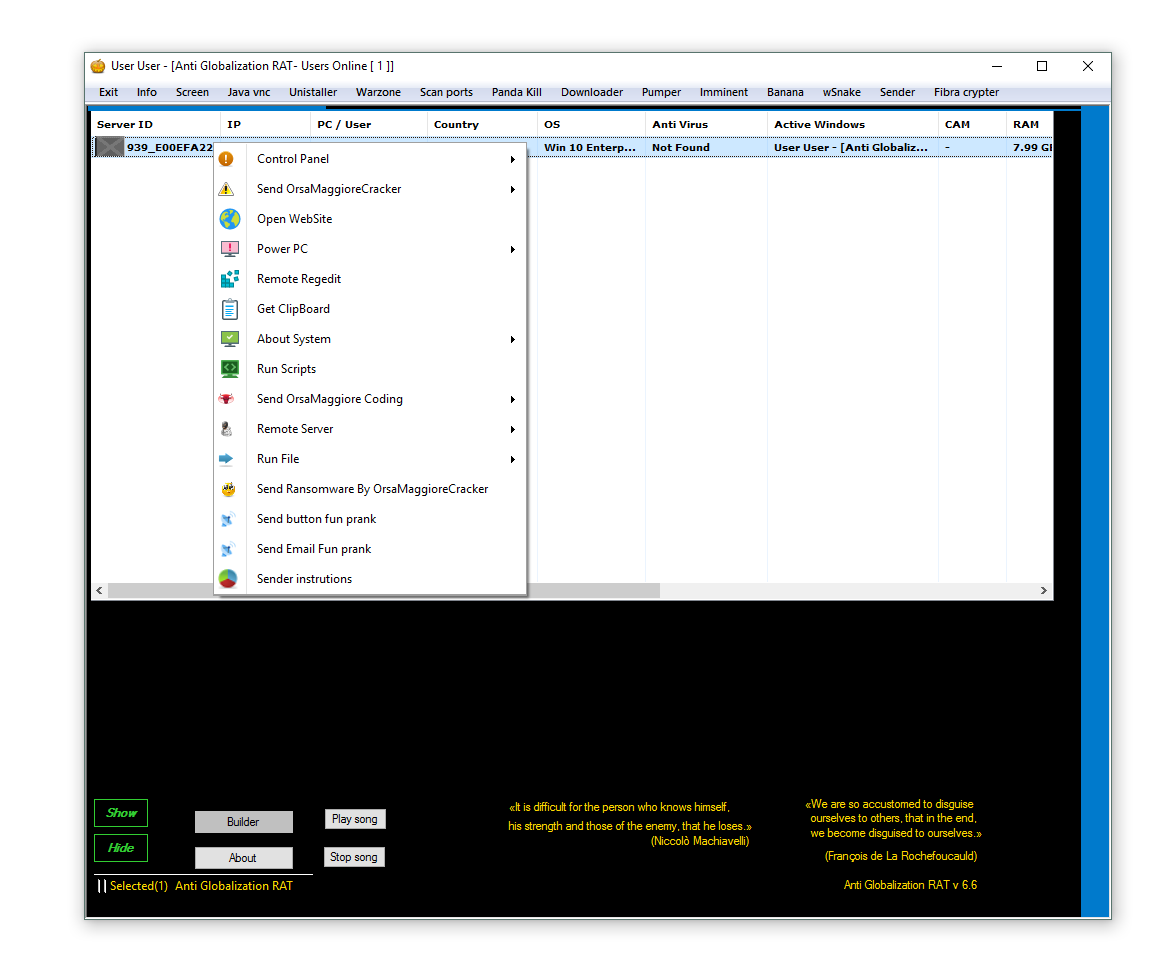
🔹 4. feature image (ZK RAT)
The main dashboard acts as the command-and-control center of QZK RAT 2026. It provides operators with a real-time overview of infected systems and attack modules.
⚙️ Features displayed in QZK RAT 2026:
- 🌍 IP Information: IP tracking allows attackers to identify victim locations, internet providers, and regional targets.
- 👤 Group, ID, Username, Operating System, Country, Date: Detailed client identification enables attackers to sort victims and prioritize valuable targets.
- 🎛️ Clients Control: The management console centralizes malware operations including ransomware deployment, remote control, and surveillance functions.
⚠️ Threat Level in QZK RAT 2026:
High – Centralized management dramatically increases the efficiency of large-scale cybercrime operations.
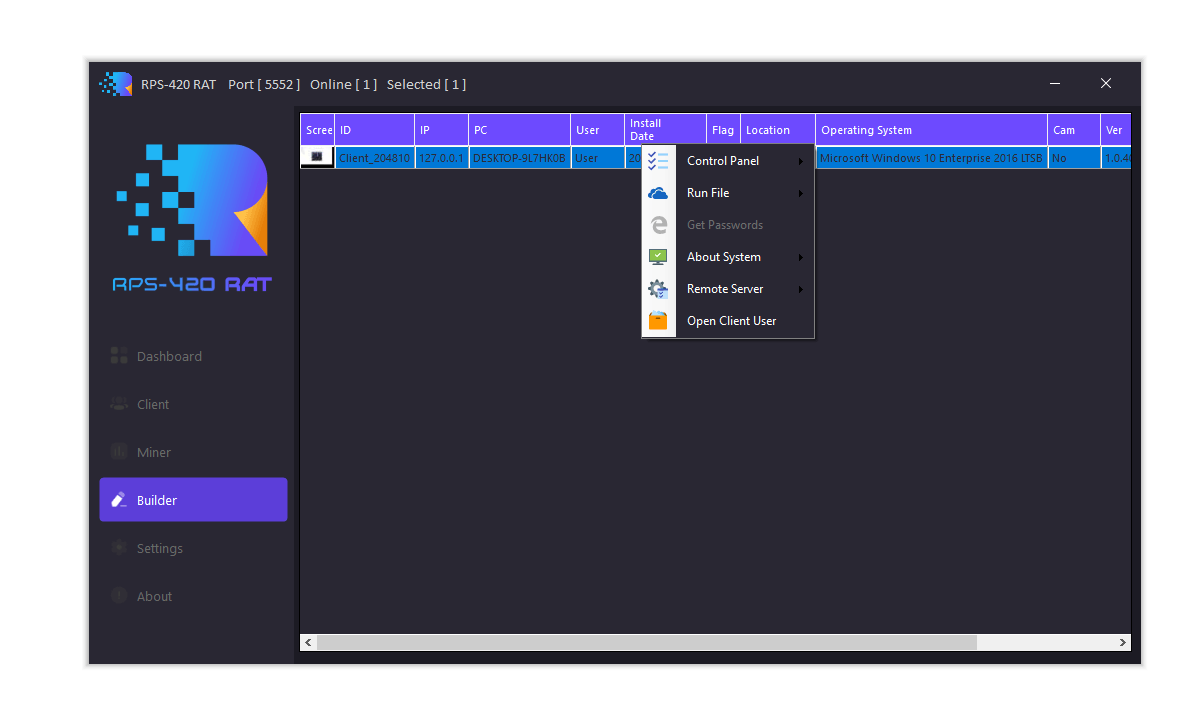
🔹 5. ZZK RAT – Hidden RDP
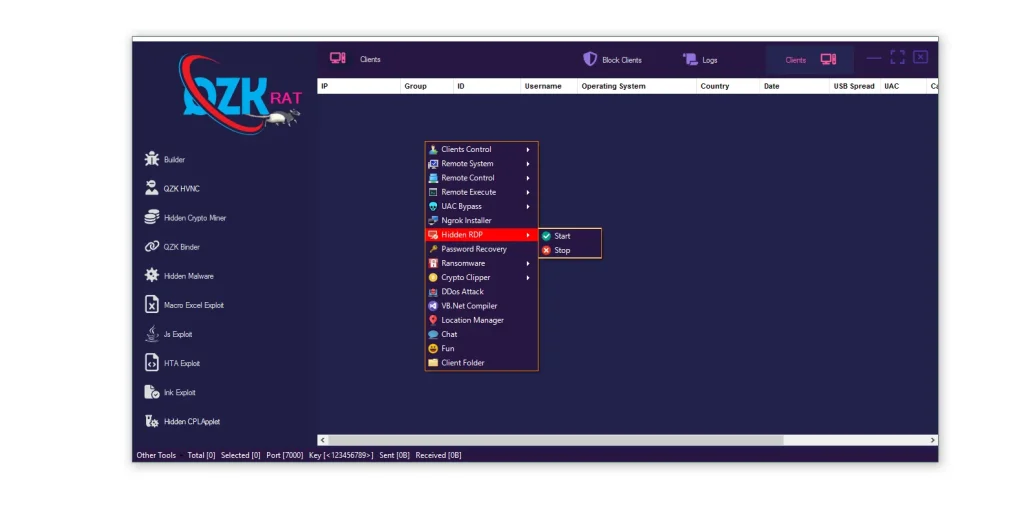
The Hidden RDP module enables stealth remote desktop access without the victim’s knowledge. This feature is commonly used for banking fraud, account takeovers, and unauthorized system administration.
⚙️ Features displayed in QZK RAT 2026:
- 🖥️ Hidden RDP: Hidden desktop sessions allow attackers to remotely control a machine while remaining invisible to the victim.
- 🧰 Builder Sidebar: The builder menu integrates multiple malware modules into one operational dashboard for streamlined attacks.
- 📊 Client Management: Sorting and filtering tools help operators organize victims by operating system, region, or infection status.
⚠️ Threat Level in QZK RAT 2026:
Critical – Hidden remote desktop functionality gives attackers near-complete control over infected systems.
🔹 6. ZK RAT – HTA Exploit
The HTA Exploit module creates malicious HTML Application files capable of executing scripts and commands on Windows systems.
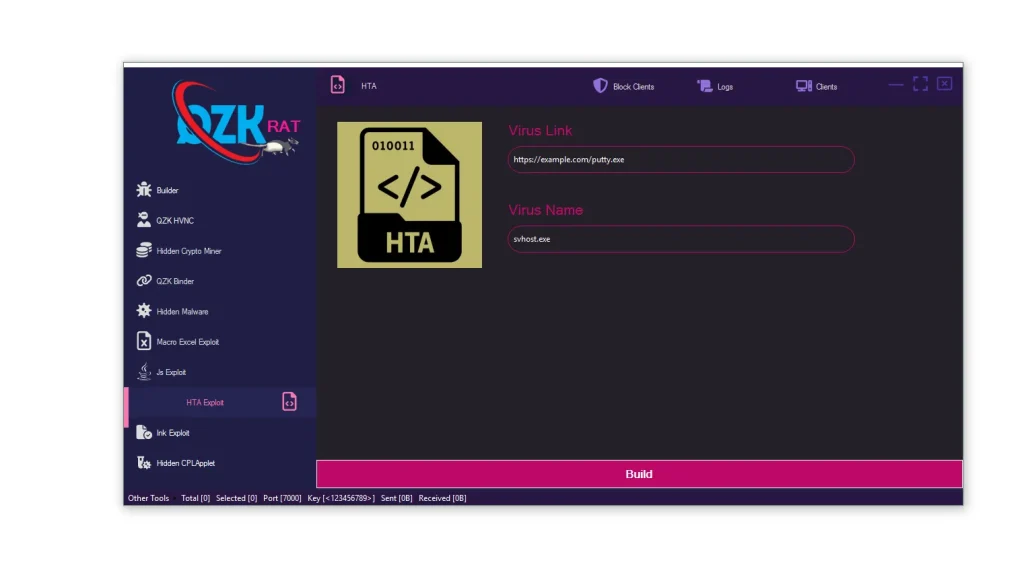
⚙️ Features displayed in QZK RAT 2026:
- 🌐 Virus Link: Attackers can define remote payload locations used to download secondary malware components.
- 📝 Virus Name: Payload renaming allows malware to impersonate legitimate software or system files.
- 🏗️ Build: The build function generates malicious HTA payloads for phishing campaigns or malicious downloads.
⚠️ Threat Level in QZK RAT 2026:
High – HTA files are dangerous because Windows can execute them using built-in scripting engines.
🔹 7. JS Exploit
The JS Exploit module generates malicious JavaScript payloads often distributed through phishing emails or compromised websites.
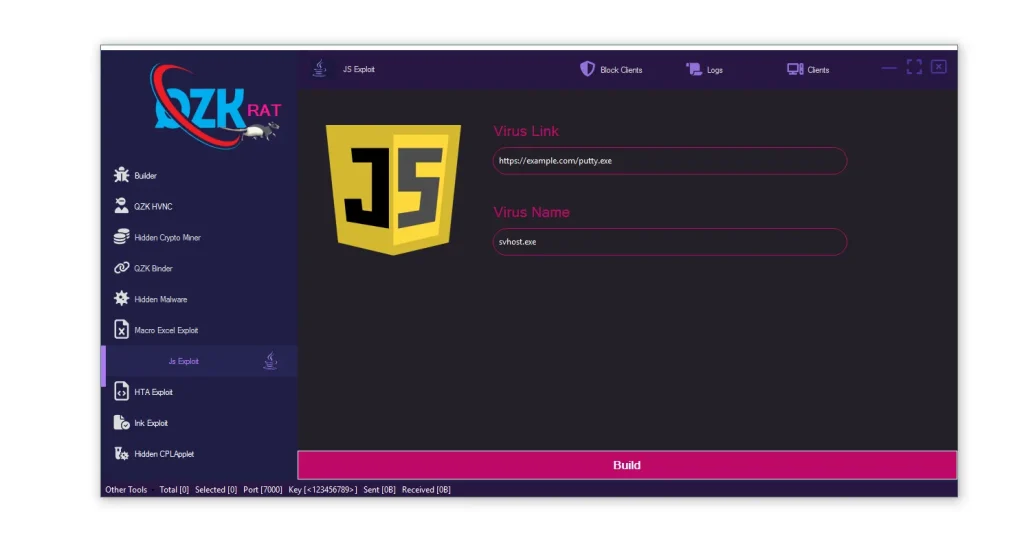
⚙️ Features displayed in QZK RAT 2026:
- 📂 Block Clients / Logs / Clients: Logging systems help malware operators track infections and campaign performance.
- 🧰 Builder Menu: Multiple exploit modules are integrated into the interface for multi-stage attack deployment.
- 🌐 Virus Link: Remote payload hosting enables flexible malware delivery without embedding large files.
- 🏗️ Build: Payload generation automates malicious script creation for cybercriminal campaigns.
⚠️ Threat Level in QZK RAT 2026:
High – JavaScript-based attacks remain effective due to widespread browser and scripting engine usage.
🔹 8. Ink Exploit (Link Exploit)
The Ink Exploit module focuses on malicious Windows shortcut files designed to execute hidden commands in the background.
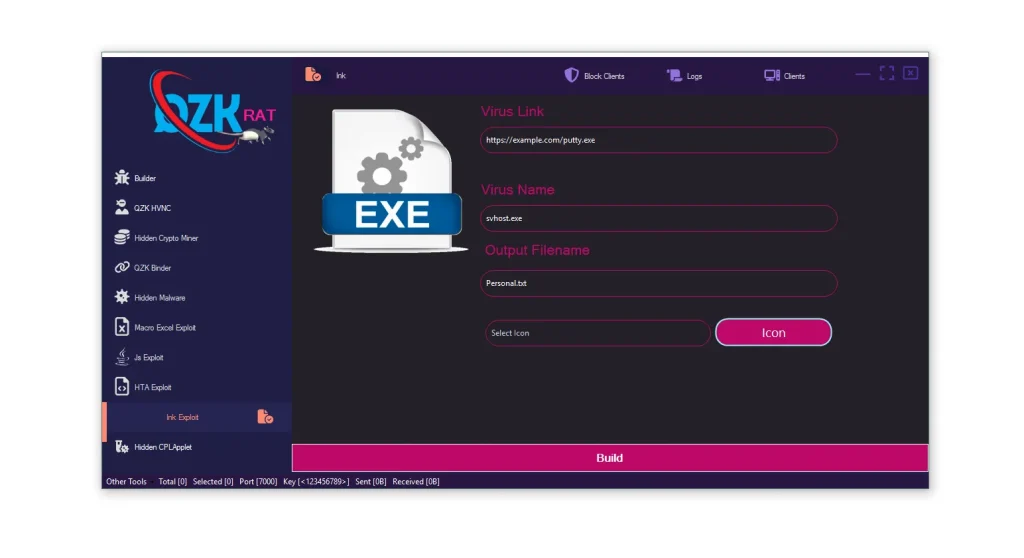
⚙️ Typical Features of Ink Exploit in QZK RAT 2026:
- 🔗 Shortcut-Based Execution: Malicious shortcut files can silently launch scripts or malware payloads without obvious warning signs.
- ⬇️ Background Downloads: Attackers use hidden commands to download secondary payloads from remote infrastructure.
- 🖼️ Legitimate-Looking Icons: Spoofed icons increase trust and encourage users to interact with malicious files.
⚠️ Threat Level in QZK RAT 2026:
High – Shortcut exploits are widely abused in phishing campaigns and removable media attacks.
🔹 9. ZKRAT – Macro Excel Exploit
The Macro Excel Exploit module creates malicious Microsoft Office documents capable of delivering malware when macros are enabled.
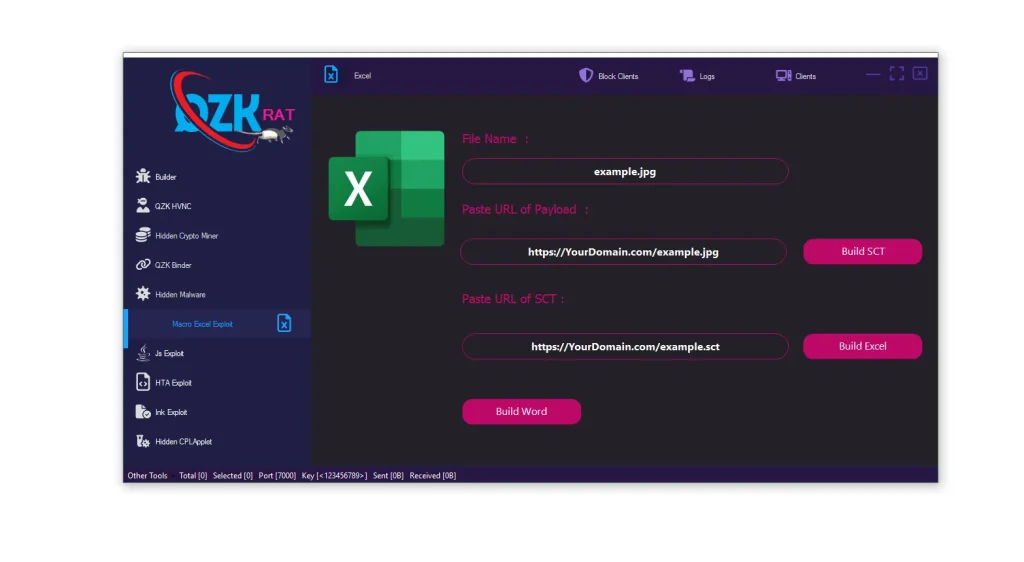
⚙️ Features displayed in QZK RAT 2026:
- 📄 File Name: Attackers disguise malicious documents as invoices, reports, or images to improve social engineering success.
- 🌐 Paste URL of Payload: Remote payload hosting allows malware to retrieve additional components after the document is opened.
- 🧩 Paste URL of SCT: Scriptlet-based delivery techniques may be used to evade traditional detection methods.
- 🏗️ Build Word / Build Excel: Automated document generation simplifies phishing campaign creation.
⚠️ Threat Level in QZK RAT 2026:
Critical – Office macro malware remains one of the most common enterprise attack vectors.
🔹 10. ZKRAT – Ransomware
The ransomware module extends QZK RAT 2026 beyond surveillance and theft by enabling file encryption and extortion operations.
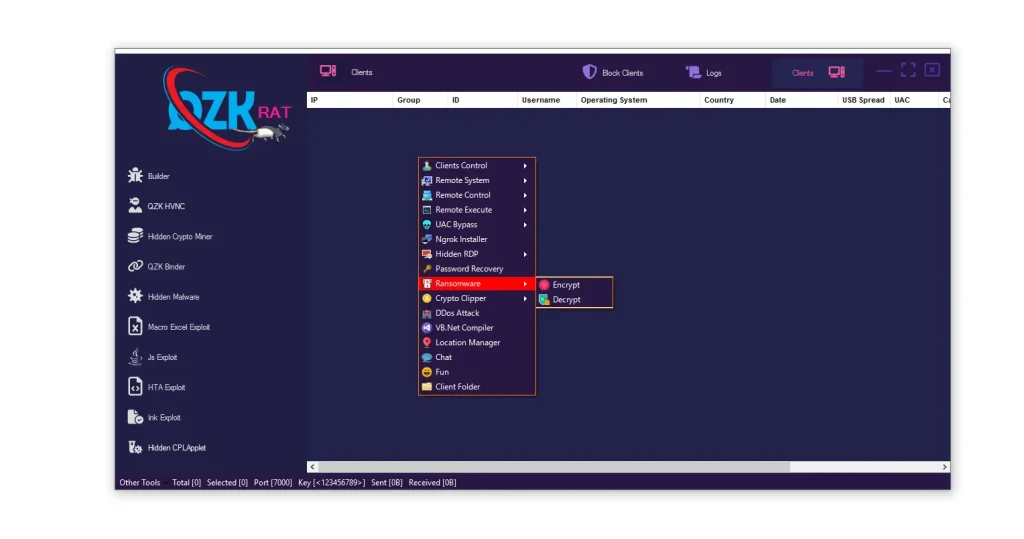
⚙️ Features displayed in QZK RAT 2026:
- 🌍 Victim Tracking: Attackers can identify systems before launching ransomware attacks.
- 🎛️ Clients Control: Centralized deployment allows rapid ransomware execution across multiple infected devices.
- 🔒 Encrypt: File encryption locks user data and business documents until ransom demands are met.
- 🔓 Decrypt: Decryption options may be used for testing or controlled recovery operations.
⚠️ Threat Level in QZK RAT 2026:
Critical – Ransomware attacks can disrupt businesses, destroy productivity, and lead to major financial losses.
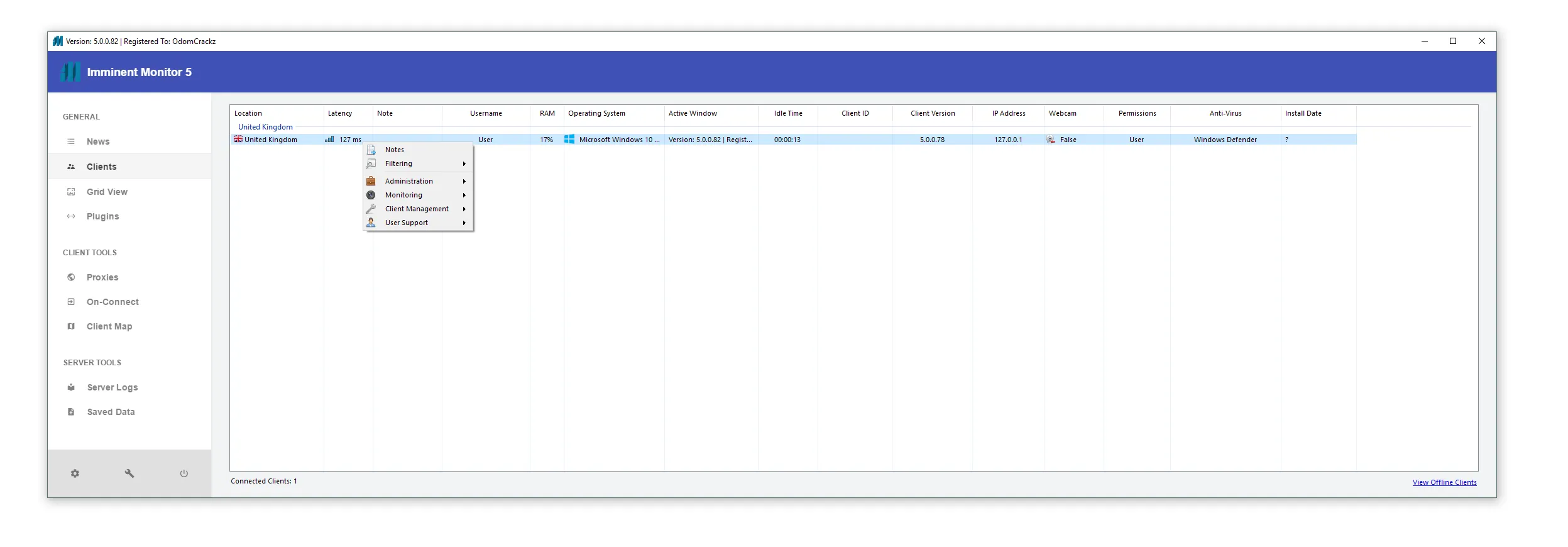
🔹 11. ZK RAT – Remote Control
The Remote Control module is one of the most powerful components of QZK RAT 2026 because it enables surveillance, remote administration, and credential theft.
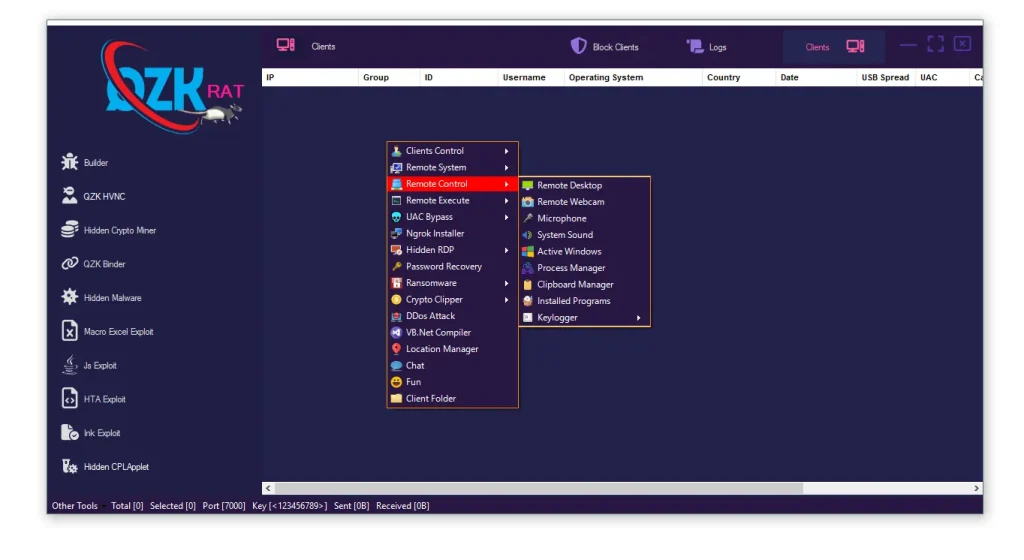
⚙️ Extended Features displayed in QZK RAT 2026:
- 🖥️ Remote System: Attackers gain direct access to system-level operations and administrative controls.
- 🎥 Remote Desktop: Full desktop viewing and interaction enables live monitoring of user activity.
- ⚡ Remote Execute: Malware operators can remotely launch commands or secondary payloads.
- 📷 Remote Webcam: Unauthorized webcam access creates major privacy and surveillance concerns.
- 🎤 Microphone: Audio recording features can capture conversations and sensitive discussions.
- 🔐 Password Recovery: Credential theft modules target saved browser passwords and authentication data.
- ⌨️ Keylogger: Keylogging functions capture usernames, passwords, and sensitive communications.
- 📍 Location Manager: IP-based geolocation helps attackers profile targets and regionalize attacks.
⚠️ Threat Level in QZK RAT 2026:
Critical – The combination of surveillance, credential theft, and remote execution makes this module highly dangerous.
🔹 12. ZK RAT – Remote Execute
The Remote Execute functionality focuses on remotely launching commands, scripts, or malware payloads on infected systems.
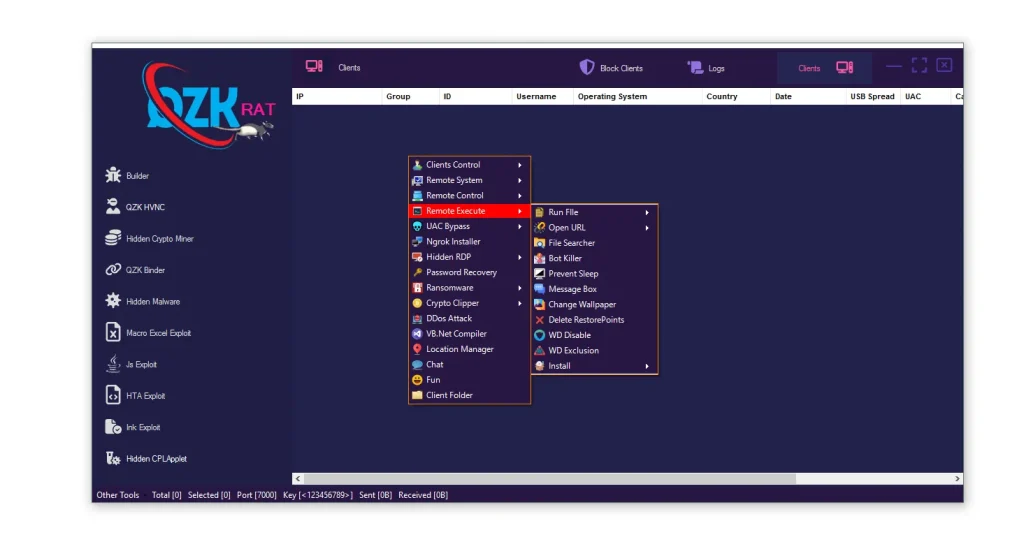
⚙️ Features displayed in QZK RAT 2026:
- 🧰 Builder Menu: Centralized controls simplify remote malware management and deployment.
- 🎛️ Clients Control: Attackers can execute commands across multiple compromised systems simultaneously.
- 📊 Logs and Filtering: Searchable fields help operators target specific regions, operating systems, or users.
⚠️ Threat Level in QZK RAT 2026:
High – Remote execution capabilities enable fast malware expansion across networks.
🔹 13. ZK RAT – Remote System
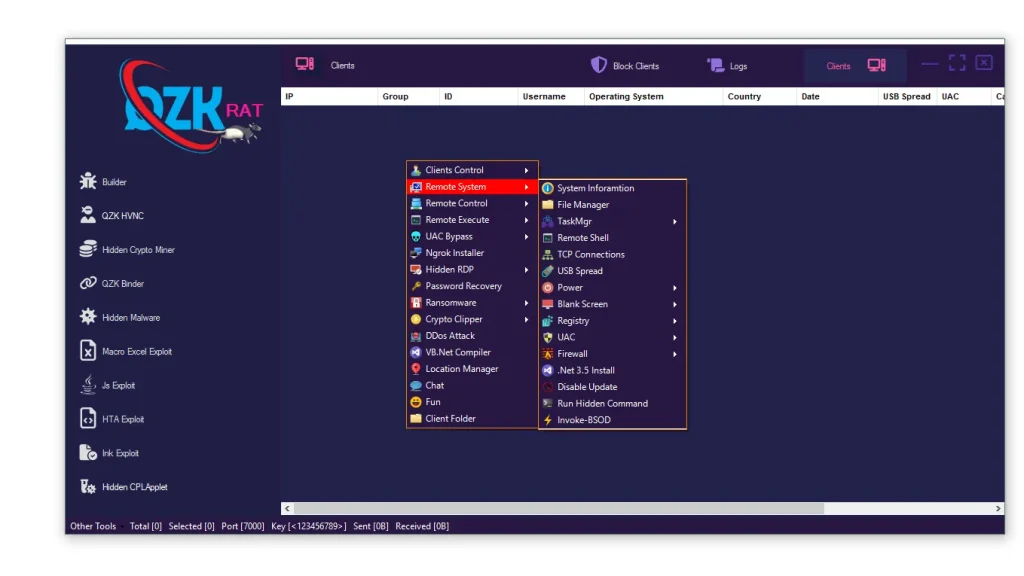
The Remote System module provides low-level administrative access to compromised Windows systems.
⚙️ Detailed Features displayed in QZK RAT 2026:
- 📁 File Manager: Attackers can upload, download, or delete files remotely from infected machines.
- ⚙️ TaskMgr: Process management features allow malware operators to terminate security tools or competing malware.
- 💻 Remote Shell: Command-line access enables advanced system manipulation and scripting operations.
- 🌐 TCP Connections: Monitoring active network connections helps attackers analyze network activity.
- 🔌 USB Spread: USB propagation features increase malware distribution through removable drives.
- 🔥 Firewall: Attackers may attempt to weaken or disable Windows security protections.
- 🧱 Disable Update: Disabling updates prevents systems from receiving important security patches.
- 💥 Invoke-BSOD: System crash capabilities may be used for sabotage or disruption.
⚠️ Threat Level in QZK RAT 2026:
Critical – Full administrative access gives attackers the ability to manipulate nearly every part of the operating system.
🔹 14. ZKR RAT – UAC Bypass
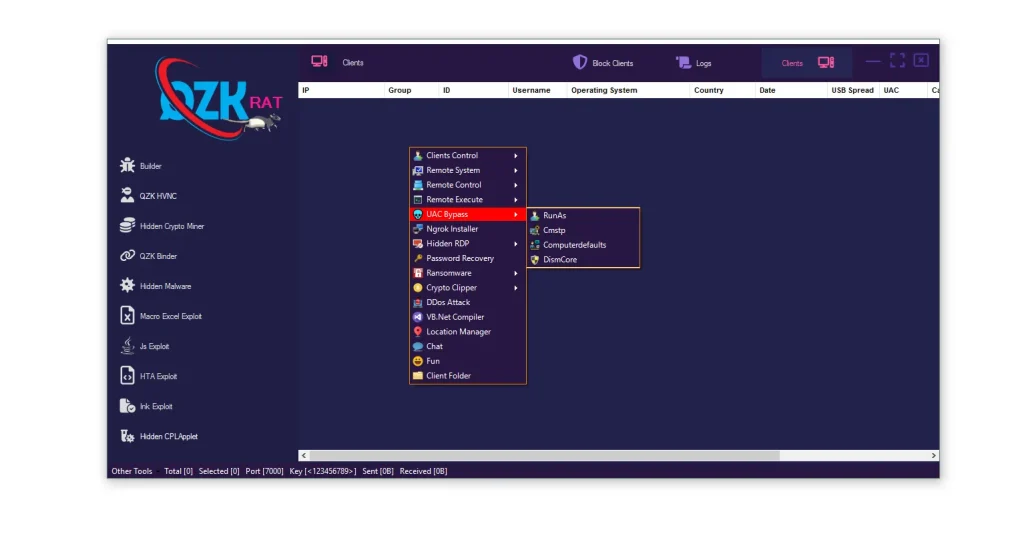
The UAC Bypass module focuses on privilege escalation techniques that help malware gain elevated access.
⚙️ Features displayed in QZK RAT 2026:
- 🧰 Builder Sidebar: Integrated attack modules simplify privilege escalation workflows.
- 📊 Client Tracking: Detailed tracking allows operators to identify systems vulnerable to privilege escalation.
- 💻 Code Editor Area: Custom scripting support enables attackers to modify payload behavior.
- 🔓 UAC Bypass: Privilege escalation helps malware operate with administrative permissions.
⚠️ Threat Level in QZK RAT 2026:
Critical – Elevated privileges allow malware to disable defenses, persist longer, and gain deeper system access.
🔹 15. Start Crypto Miner Builder
The Start Crypto Miner Builder section provides a detailed interface for creating customized hidden cryptocurrency miners.
⚙️ Features displayed in QZK RAT 2026:
- ⛏️ Start Crypto Miner Builder: This interface centralizes miner configuration and deployment management.
- 📂 Block Clients / Logs / Clients: Logging systems help operators monitor mining activity and infected devices.
- ⚙️ Main, Miners, Startup, Assembly, Icon, Options, Build: Each configuration tab controls specific mining behaviors including stealth, persistence, and evasion.
- ➕ Add / Edit / Remove: Miner profile management allows customized mining strategies for different campaigns.
- 💾 Save / Load: Configuration storage enables rapid reuse of miner settings.
⚠️ Threat Level in QZK RAT 2026:
Critical – Persistent mining malware can severely impact enterprise hardware and operational performance.
🌐 QZK RAT 2026: Network Indicators
The interface screenshots reveal several operational indicators useful for cybersecurity teams and threat hunters.
| Indicator | Significance |
|---|---|
| Port Usage | Potential command-and-control communication channel |
| Authentication Keys | Possible malware configuration signatures |
| Sent / Received Counters | Traffic monitoring and operational statistics |
Security teams should monitor unusual outbound traffic, suspicious persistence behavior, and unauthorized remote access activity.
🧰 QZK RAT 2026: Complete Builder Module List
| Module Name | Purpose |
| QZK HVNC | Hidden remote desktop access |
| Hidden Crypto Miner | Silent cryptocurrency mining |
| QZK Binder | File binding and payload hiding |
| Hidden Malware | Stealth malware generation |
| Macro Excel Exploit | Malicious Office document creation |
| JS Exploit | JavaScript malware generation |
| HTA Exploit | HTA payload creation |
| Ink Exploit | Malicious shortcut generation |
| Hidden CPLExploit | Malicious Control Panel payloads |
⚠️ Threat Analysis & Verdict for QZK RAT 2026
Overall Severity Level: Critical
QZK RAT 2026 represents a highly dangerous malware ecosystem because it combines multiple monetization and attack methods into one framework. Instead of relying on a single attack vector, operators can switch between ransomware deployment, cryptocurrency theft, remote surveillance, credential harvesting, and hidden mining.
🚨 Why QZK RAT 2026 is Particularly Dangerous:
- 🧩 All-in-One Design: Attackers can manage multiple malicious operations from one centralized platform, reducing operational complexity.
- 👨💻 User-Friendly Interface: The graphical interface lowers the technical barrier for cybercriminals with limited coding knowledge.
- 🛡️ Evasion Features: Obfuscation, hidden execution, and persistence mechanisms increase resistance against traditional antivirus tools.
- 💰 Multiple Revenue Streams: Operators can profit through ransomware, crypto theft, credential sales, and mining activities simultaneously.
- 🔌 USB Propagation: Removable media spreading capabilities increase infection reach inside enterprise environments.
🛡️ Defensive Recommendations Against QZK RAT 2026
🔹 For Network Administrators:
🚫 Application Control:
Restrict execution of potentially dangerous file types such as HTA, JS, and shortcut-based payloads where possible.
🌐 Network Hardening:
Monitor outbound traffic for suspicious command-and-control behavior and unauthorized remote access sessions.
🔎 DNS Filtering:
Implement DNS filtering and domain reputation analysis to block malicious infrastructure.
🔹 For Endpoint Security Teams:
🧠 Behavioral Monitoring:
Behavior-based detection systems are more effective than signature-only antivirus against modular malware frameworks.
📄 Macro Policies:
Disable unnecessary Office macros and restrict unsigned document execution across enterprise environments.
🔐 UAC Configuration:
Maintain strong Windows security settings and minimize unnecessary administrative privileges.
🔹 For Individuals:
💳 Crypto Wallet Hygiene:
Always verify cryptocurrency wallet addresses before transferring funds.
🔌 USB Security:
Disable AutoRun features and avoid connecting unknown removable devices.
📧 Email Vigilance:
Avoid opening suspicious attachments or enabling macros from unknown senders.
📌 IOCs (Indicators of Compromise) for QZK RAT 2026
| Type | Indicator |
| Suspicious Traffic | Unusual outbound connections |
| Fake System Names | Misspelled Windows process names |
| Registry Changes | Unauthorized startup persistence |
| Malicious File Types | HTA, JS, LNK, SCT payloads |
Download QZK RAT 2026
Virus Total Report
https://www.virustotal.com/gui/file/c62b713747d6cff351f1088346caeb4799aa5718bbf073c37f58011e9abc99c7✅ Conclusion: The Evolution of QZK RAT 2026
QZK RAT 2026 demonstrates how modern malware frameworks are evolving into highly modular cybercrime ecosystems. By combining remote access, ransomware, clipboard hijacking, hidden mining, credential theft, and persistence features into a single platform, this malware significantly increases the potential impact of cyberattacks.
For organizations in the United States and Europe, understanding the operational structure and behavior of threats like QZK RAT 2026 is essential for building stronger defensive strategies. Modern cybersecurity defenses should focus on behavioral analysis, endpoint detection, network monitoring, and employee awareness training to reduce the risk of compromise.
As modular malware frameworks continue evolving, defenders must prioritize proactive threat hunting, incident response readiness, and layered security architectures.
❓ FAQs About QZK RAT 2026
🔹 What is QZK RAT 2026?
QZK RAT 2026 is a modular Remote Access Trojan framework that combines remote control, credential theft, ransomware, crypto clipping, and hidden mining capabilities.
🔹 Why is QZK RAT 2026 considered dangerous?
The malware includes multiple attack modules that allow cybercriminals to steal data, monitor victims, encrypt files, and generate cryptocurrency revenue.
🔹 How does QZK RAT 2026 spread?
The malware commonly spreads through phishing emails, malicious Office documents, shortcut files, JavaScript payloads, and social engineering attacks.
🔹 Can antivirus software detect QZK RAT 2026?
Traditional antivirus may detect known variants, but heavily modified samples can evade signature-based detection. Behavioral monitoring is more effective.
🔹 Which operating systems are targeted by QZK RAT 2026?
The malware primarily targets Microsoft Windows systems.
🔹 What industries are most at risk?
Businesses handling financial data, cryptocurrency operations, healthcare records, and remote workforce infrastructure are common targets.
🔹 How can organizations defend against QZK RAT 2026?
Organizations should implement endpoint detection solutions, network segmentation, employee security awareness training, and strong access control policies.
🔹 Is QZK RAT 2026 used in ransomware attacks?
Yes. The framework includes ransomware deployment functionality capable of encrypting victim files.
🔹 Does QZK RAT 2026 steal cryptocurrency?
Yes. Its crypto clipper module can replace copied wallet addresses to redirect transactions.
🔹 What makes modular malware frameworks dangerous?
Modular malware allows attackers to customize capabilities, switch monetization methods, and rapidly adapt to new security defenses.
Disclaimer: This article is intended strictly for cybersecurity education, malware awareness, defensive analysis, and threat intelligence research. Unauthorized deployment or distribution of malware is illegal and unethical.