The RPS420 RAT 2026 Cracked variant has recently been observed circulating in underground cybercrime ecosystems. As a Remote Access Trojan (RAT), it is designed to provide full unauthorized control over infected systems while integrating advanced stealth, surveillance, and cryptojacking capabilities.
From a cybersecurity perspective, this malware represents a multi-functional attack framework, combining:
- Remote system control
- Credential theft
- Anti-analysis evasion
- Cryptocurrency mining
- Botnet capabilities
⚙️ RPS420 RAT Builder Analysis (Malware Configuration Module)
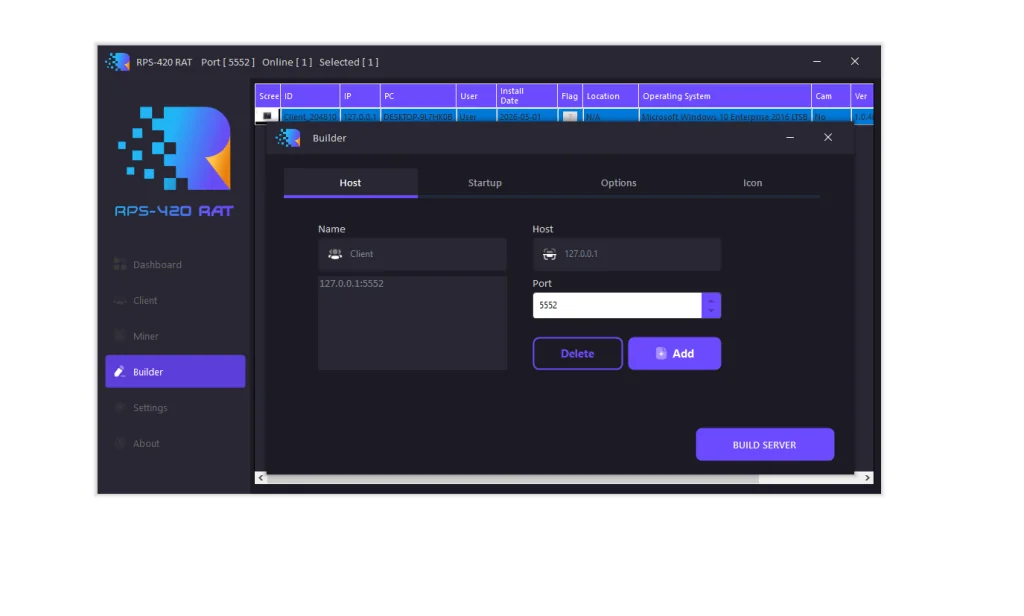
The builder module is the core component responsible for generating the malicious payload. Security analysis shows it is heavily focused on evasion, persistence, and disabling defensive tools.
🧩 Key Builder Capabilities
The RPS420 RAT builder includes the following suspicious functionalities:
🕶️ Stealth Mechanisms
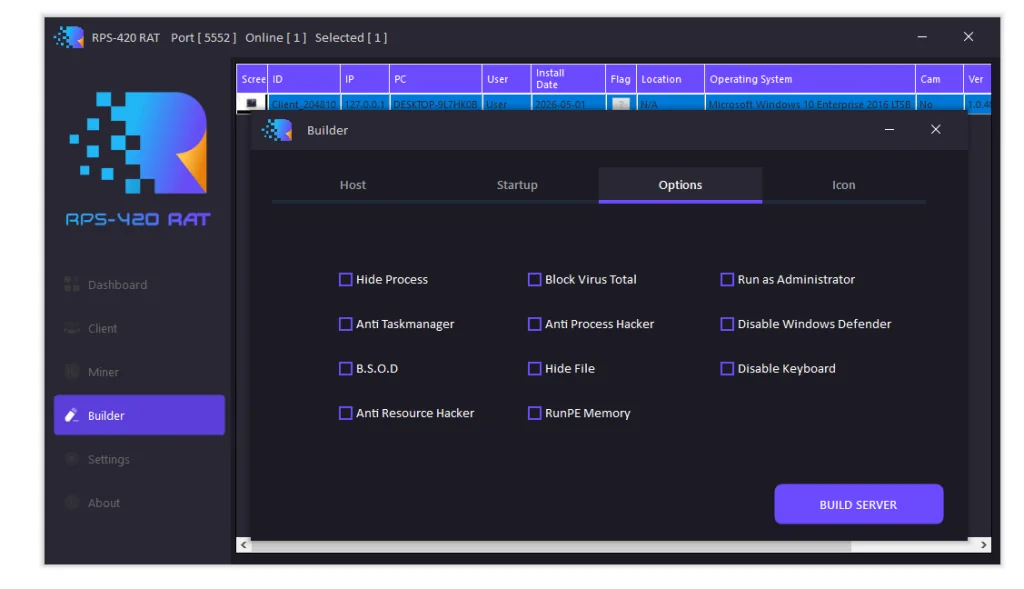
- Hide process activity from Task Manager
- Hide malware files in system directories
- Anti-Process monitoring tools blocking
🧪 Anti-Analysis Protection
- Block VirusTotal uploads
- Anti-Resource Hacker protection
- Disable debugging and reverse engineering attempts
🛑 Security Disruption Features
- Disable Windows Defender
- Trigger system instability (BSOD-like behavior)
- Block security monitoring tools
💾 Execution Techniques
- RunPE memory execution (fileless execution style)
- Automatic administrator privilege escalation
⌨️ Surveillance Features
- Keylogging functionality for input capture
🧠 Security Insight
These capabilities indicate that the malware is designed for high stealth persistence, making detection and removal significantly more complex without advanced EDR solutions.
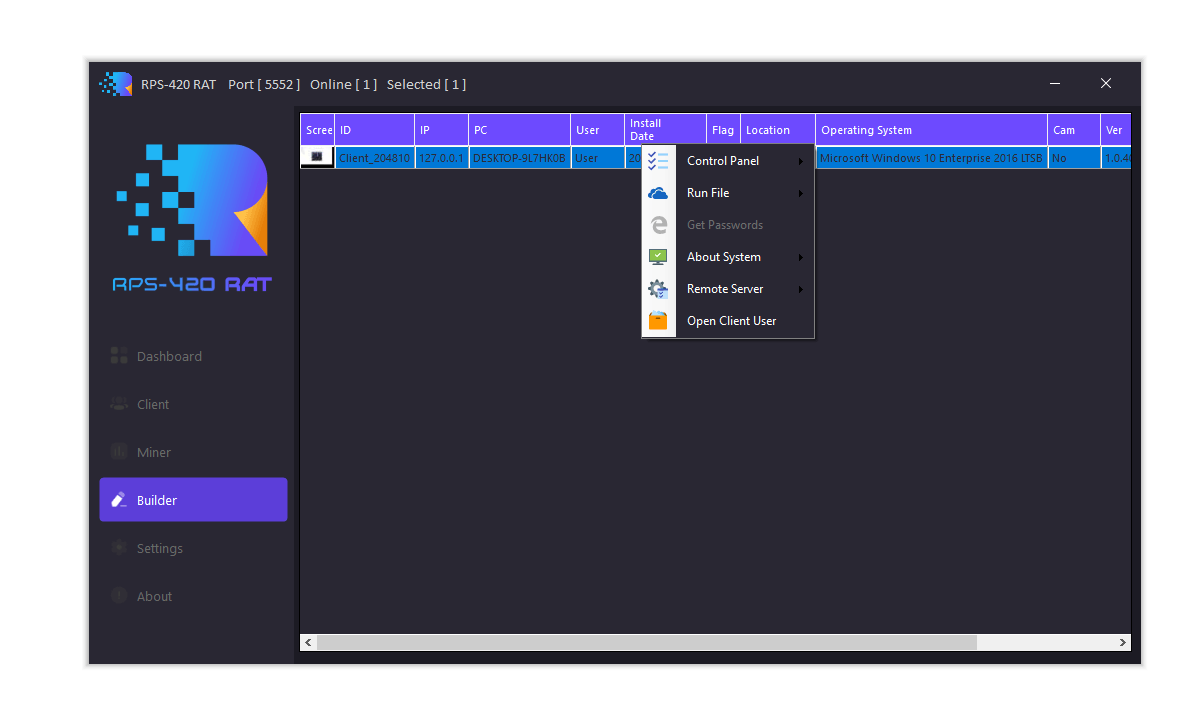
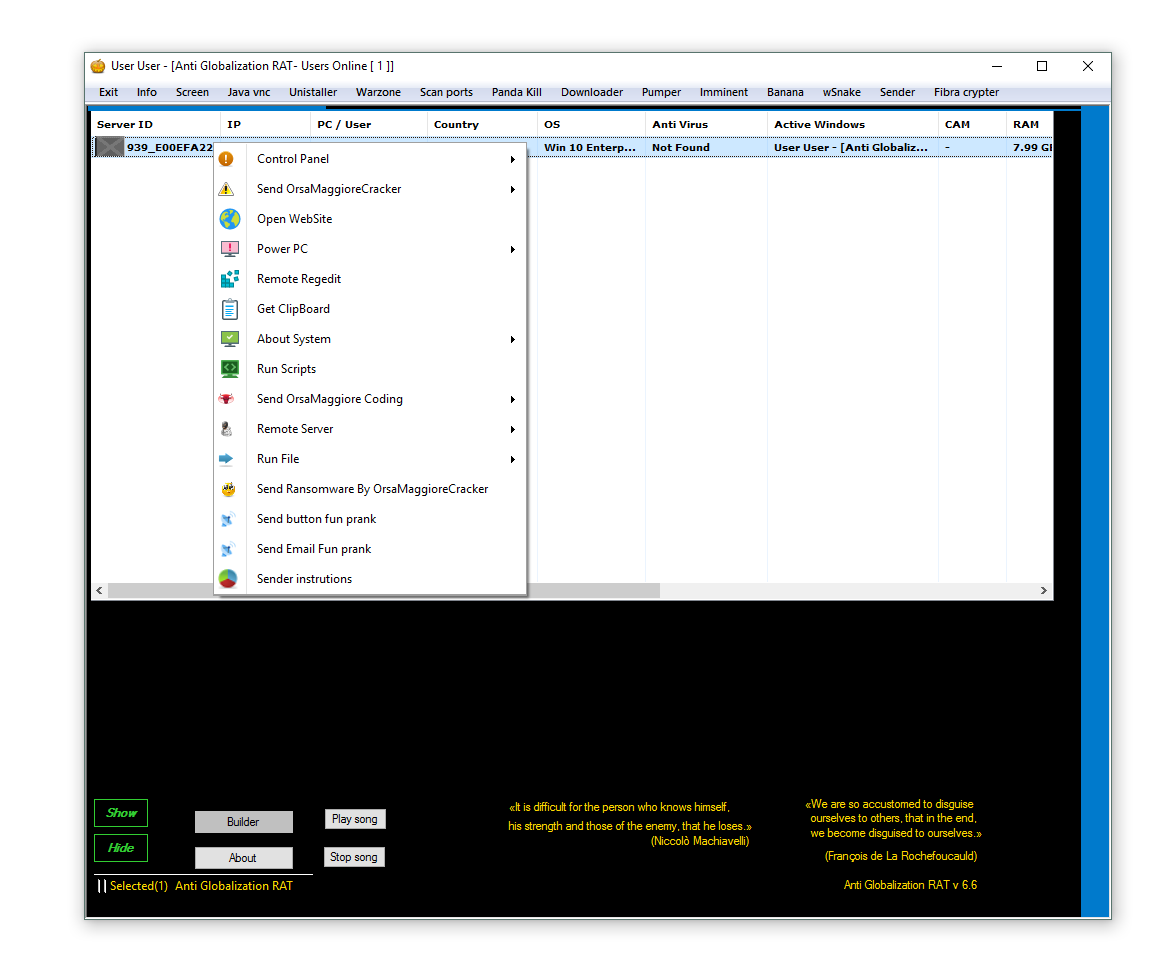
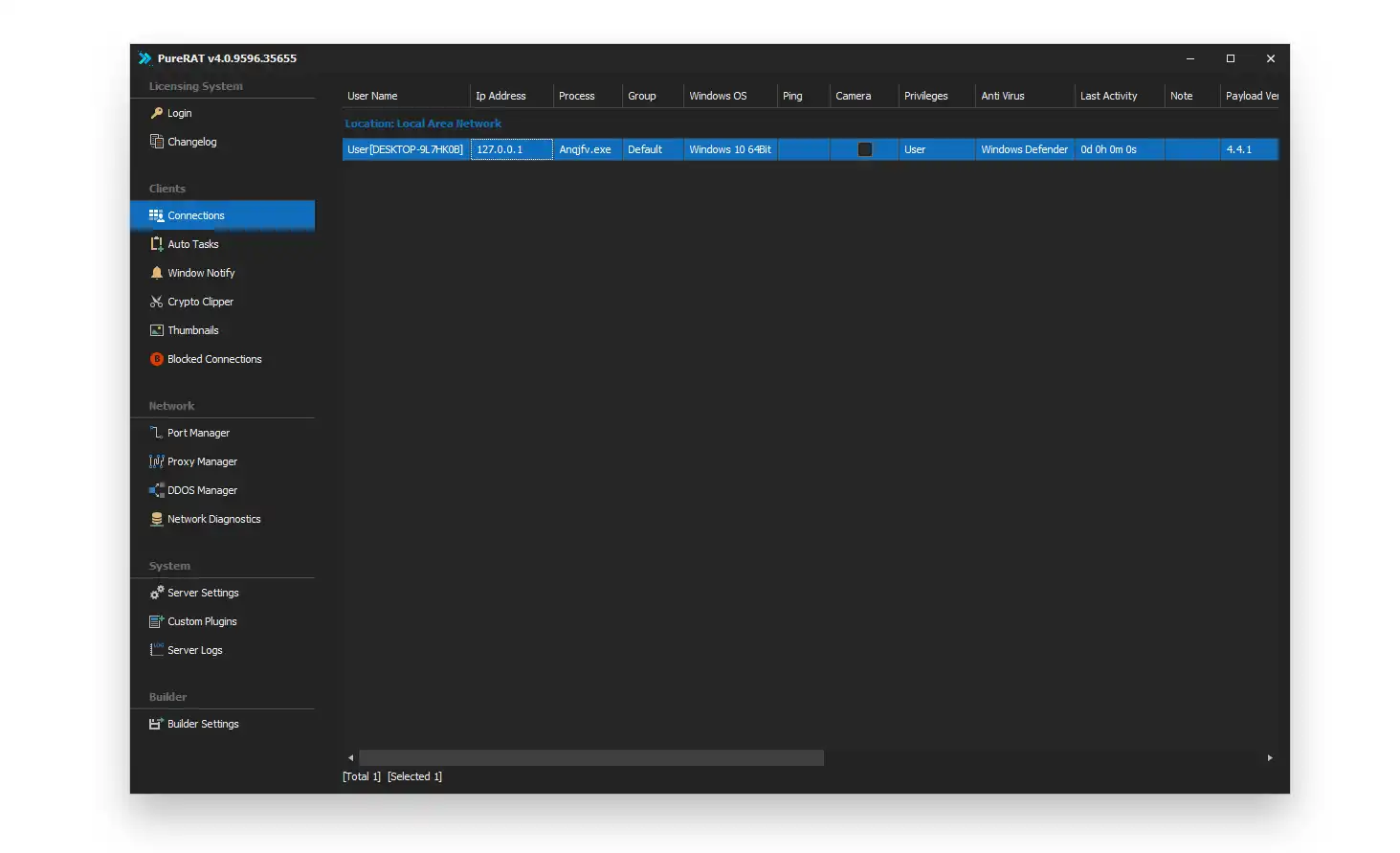
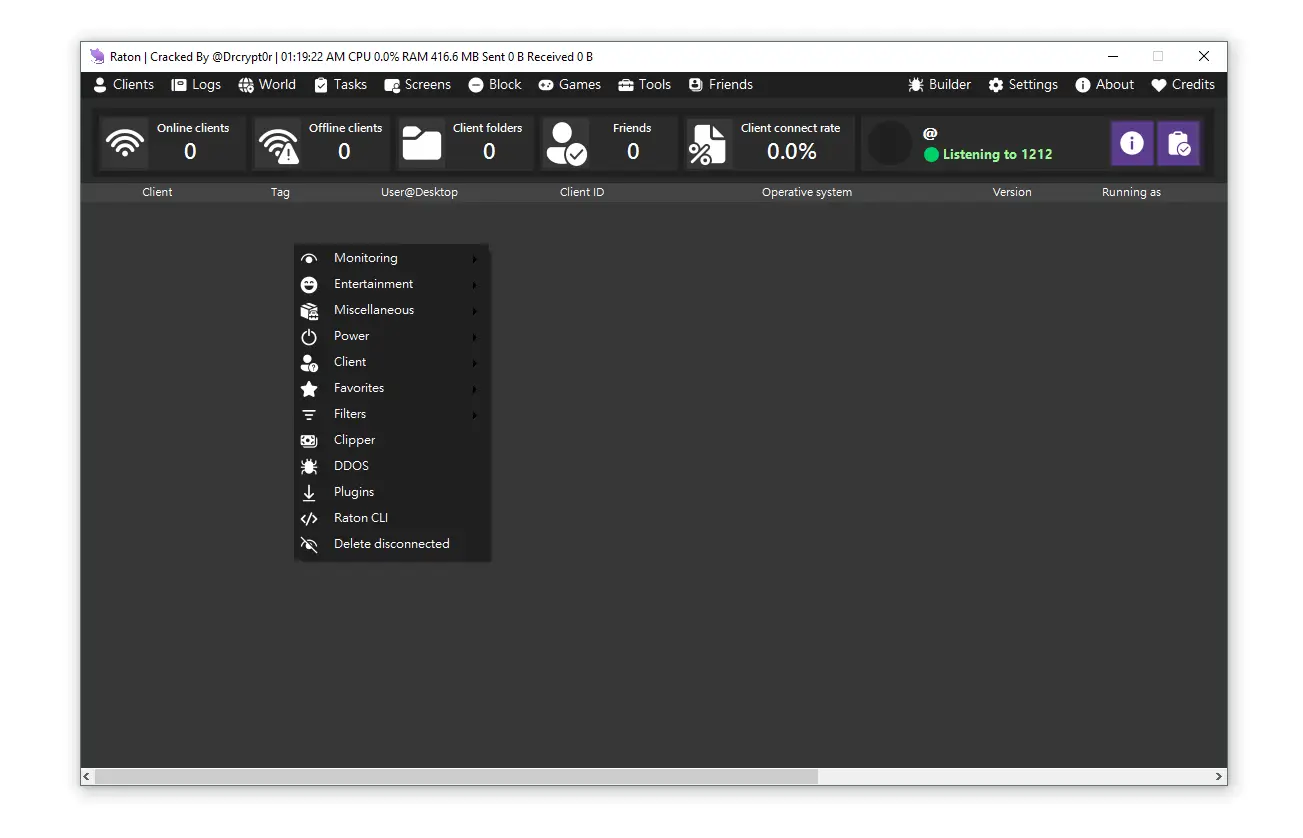
🖥️ Control Panel (Command & Control Center)
The RPS420 RAT control panel acts as a centralized management dashboard for infected devices, commonly known as a C2 (Command and Control) interface.
📊 Victim Management Dashboard
Each infected system is tracked using:
- IP address tracking
- Computer and user name identification
- Operating system version detection
- Installation timestamp
- Geographic location mapping
- Camera availability status
- Client version monitoring
👉 Internal Link: [How C2 Servers Work in Cyber Attacks]
🧰 Remote Administration Functions
The control panel enables extensive remote control capabilities:
💻 System Control
- Execute files remotely
- Open system directories
- Launch reverse shell access
🔐 Data Theft Operations
- Extract saved browser passwords
- Collect system and hardware information
📡 Monitoring Tools
- Keylogging module
- Live desktop viewing (remote access interface)
- Victim interaction chat system
🌐 Botnet Features
- DDoS attack capability using infected machines
🧠 Security Insight
This level of control indicates that RPS420 RAT functions not just as malware, but as a full botnet orchestration platform.
⛏️ XMR Miner Module (Cryptojacking Component)
One of the most financially motivated components of RPS420 RAT 2026 Cracked is its integrated Monero (XMR) mining system.
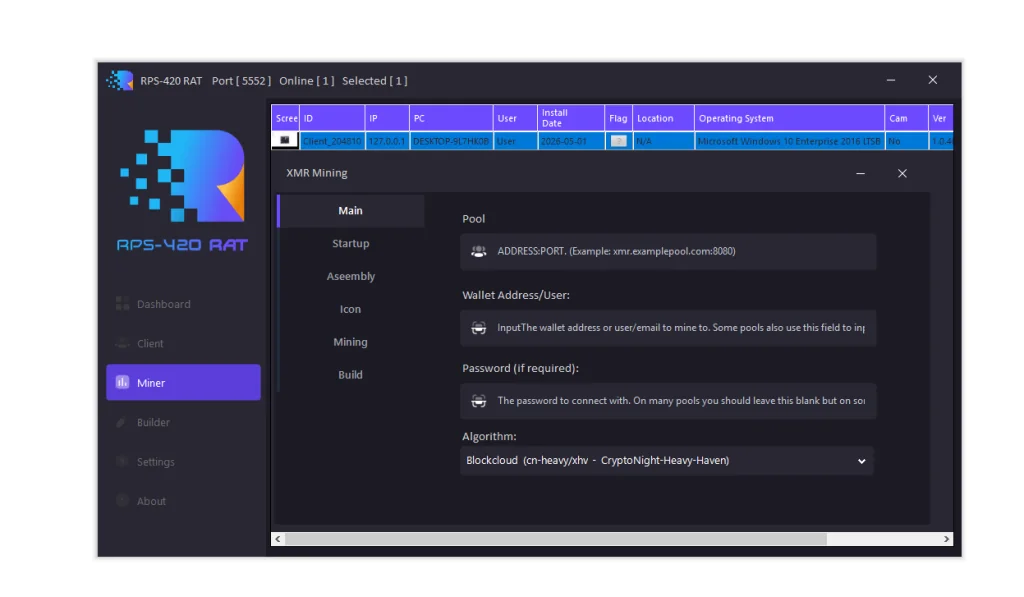
💰 Mining Configuration Elements
- Custom mining pool configuration
- Wallet address setup for payouts
- Worker identification parameters
- CPU-optimized mining algorithm selection
⚠️ Impact on Victim Systems
Infected machines often experience:
- High CPU usage (constant load)
- Increased electricity consumption
- Severe performance degradation
- Reduced hardware lifespan
👉 Internal Link: [What is Cryptojacking Malware?]
🧠 Security Insight
This module reflects a growing trend in malware evolution where attackers prioritize silent financial exploitation over immediate system destruction.
🧪 Technical Profile of RPS420 RAT 2026 Cracked
Based on observed behavior, this malware is typically deployed against:
- Windows 10 Enterprise LTSB systems
- Machines with outdated security patches
- Environments lacking endpoint detection systems
📌 Key Characteristics
- Modular malware architecture
- Fileless execution support
- Multi-vector attack design
- Botnet + spyware hybrid functionality
⚠️ Risk Factor
The “cracked” distribution increases the risk of:
- Modified malicious builds
- Hidden secondary backdoors
- Uncontrolled attacker variants
🛑 Detection & Defense Strategies
Organizations and individuals should implement layered security controls to defend against threats like RPS420 RAT.
🔐 Network Security Measures
- Monitor unusual outbound connections
- Block unknown or suspicious ports
- Implement intrusion detection systems (IDS)
🖥️ Endpoint Protection
- Use modern EDR solutions with behavioral detection
- Monitor memory injection patterns
- Detect unauthorized process spawning
⚙️ System Hardening
- Disable PowerShell where unnecessary
- Restrict WMI access
- Apply least privilege access policies
📊 Performance Monitoring
- Track unexplained CPU spikes
- Monitor persistent background processes
- Analyze abnormal system resource usage
👉 Internal Link: [Best Practices for Malware Detection in Enterprise Systems]
🧠 Threat Intelligence Summary
The RPS420 RAT 2026 Cracked malware represents a modern evolution of Remote Access Trojans, combining multiple attack vectors into a single framework:
- Remote system control (spyware capabilities)
- Credential theft and surveillance
- Cryptojacking via XMR mining
- Botnet and DDoS infrastructure
- Advanced anti-analysis techniques
🚨 Key Risk Statement
Its modular design and cracked distribution significantly increase the likelihood of widespread misuse by low-skill threat actors.
Download RPS420 RAT 2026 Cracked
🧭 Conclusion
The emergence of RPS420 RAT 2026 Cracked highlights the continued evolution of malware toward multi-functional cybercrime platforms. Its combination of stealth, monetization, and control capabilities makes it a serious concern for cybersecurity professionals.
Proactive monitoring, endpoint protection, and network anomaly detection remain essential in defending against such threats.
⚠️ Disclaimer
This article is intended strictly for cybersecurity education and threat intelligence awareness. It does not promote or support any illegal activity. Unauthorized access to systems is a criminal offense under international cybercrime laws.